A Pentest Wednesday® Story
Security programs rarely fail because controls are missing. They fail because what looks secure on the surface hasn’t been tested where it matters.
At a large organization operating within the defense industrial base, security is not theoretical. The environment underpins manufacturing, logistics, and supply chain operations where reliability matters and disruption carries real consequences.
On paper, the security program reflected that responsibility.
Endpoint detection was deployed across the enterprise. Email security was tuned. Firewalls were in place. Vulnerability scans were running. Patch cycles were consistent.
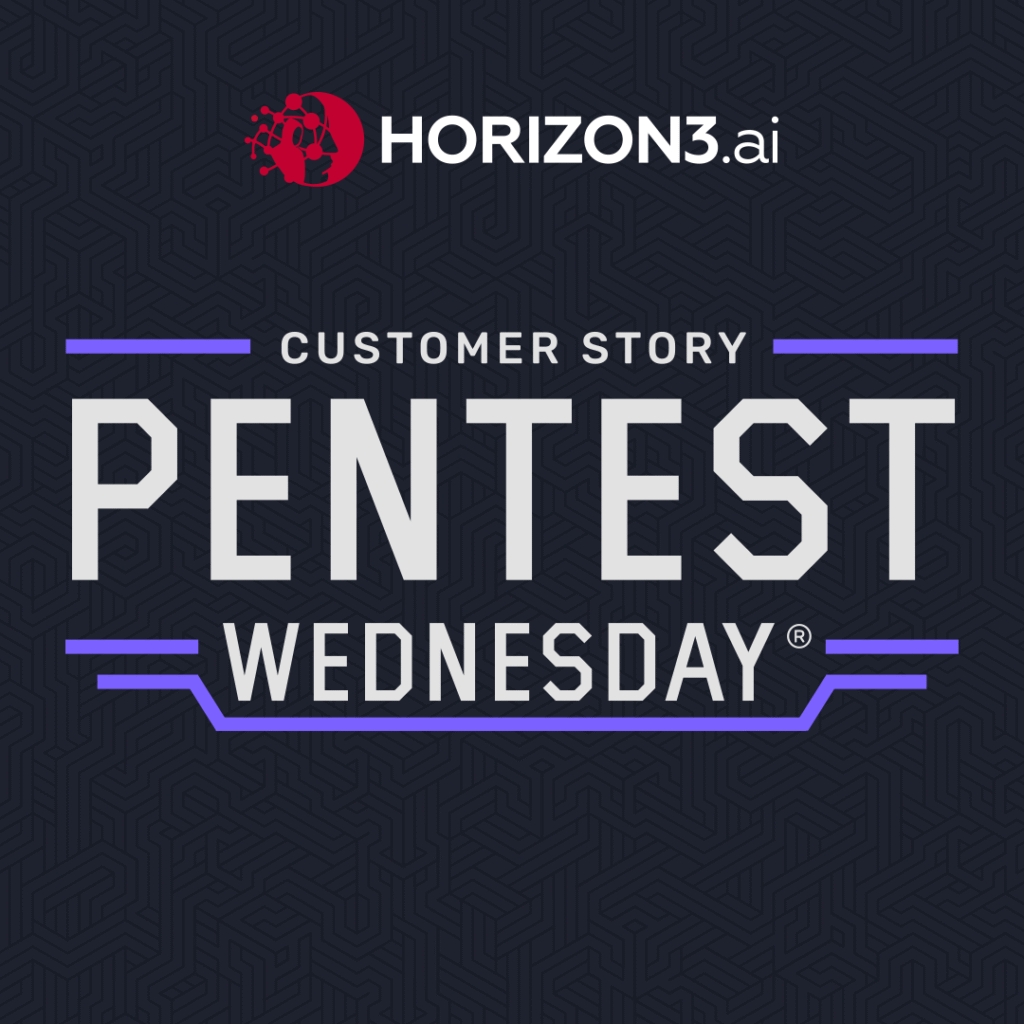
External penetration testing was performed regularly using NodeZero® to meet compliance requirements, with results consistently showing zero impacts and only a few minor weaknesses.
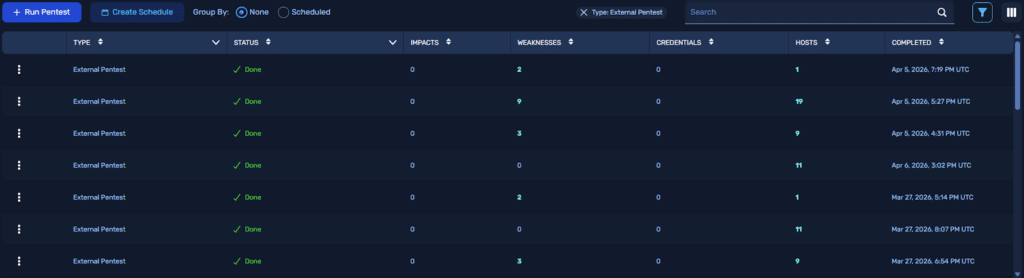
Figure 1: Repeated external pentests suggesting a strong external security posture.
From an external perspective, nothing appeared out of place. The organization had every reason to believe its defenses were working as intended.
But external validation only answers one question: can an attacker get in?
It does not answer the more important question: what happens if they already are?
Outcomes at a Glance
- 745 EDR alerts triggered during a single test
- Full system compromise achieved despite active controls
- Internal testing revealed attack paths not visible from an external perspective
- Starting from a credentialed foothold led to rapid domain compromise
- Targeted remediation eliminated high-risk attack paths and reduced impact
Impact
To answer that question, the Information Security Manager and acting CISO ran an internal test. The goal was straightforward: understand what would actually happen if an attacker gained a foothold inside the environment.
The first signal came quickly.
“Our EDR sent 745 emails overnight when the pentest kicked off… complete information system compromise.”
From a monitoring standpoint, the system responded as designed. Alerts fired at scale. The SOC escalated activity immediately, even calling in the early hours of the morning to confirm whether the behavior was expected.
But as the test unfolded, it became clear that detection alone was not the issue.
The attacker was still moving.
What NodeZero revealed was not just a stream of alerts, but a connected path to full compromise.
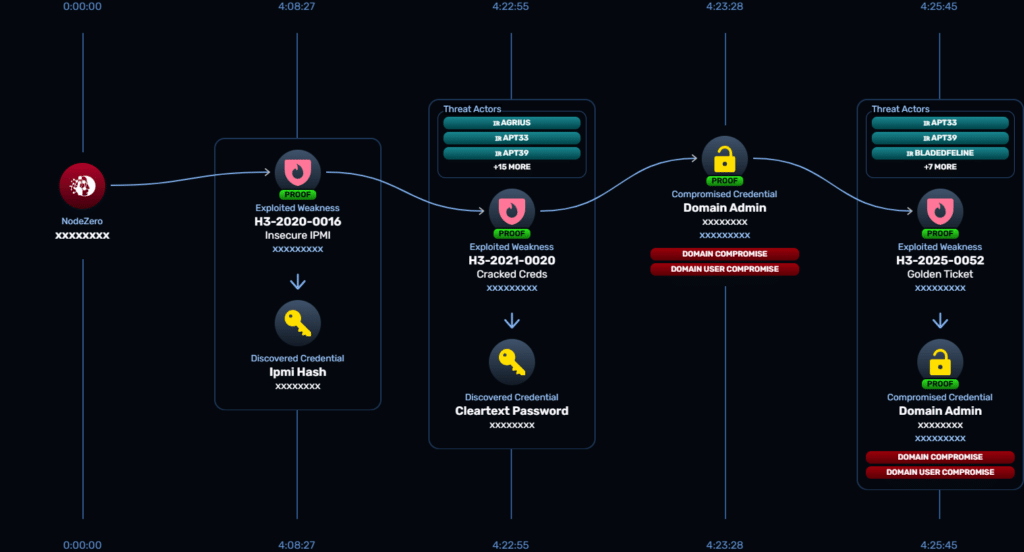
Figure 2: NodeZero mapped the full attack path from initial access to domain compromise, revealing how quickly an attacker could escalate privileges and move laterally through the environment.
The path wasn’t complex — it was the sequence that made it powerful. One exposed service led to credential access, credentials enabled lateral movement, and within hours, NodeZero escalated to full domain control.
“Something may otherwise seem innocuous, but it leads to credential loss… and then you can leverage another vulnerability and really expand from there.”
This was not a theoretical chain. It was executed end-to-end.
Internally, there was hesitation.
“I was literally the only manager in IT chasing this. The others were insisting it was a false positive.”
That reaction reflected a common challenge. When alert volume is high and previous events have not resulted in visible impact, teams become conditioned to question severity. Without a clear view of how activity connects, it is difficult to distinguish noise from real risk.
What changed was not the number of alerts. It was the clarity of the outcome.
“It did shake the IT department… they dedicated a senior server admin to resolve the vulnerabilities.”
Once the full path was visible, how access was gained, how credentials were used, and how systems were reached, the conversation shifted. The question was no longer whether the alerts were real.
It was whether the environment could withstand a real attack.
Background
The security lead was not starting from scratch. The program was already aligned to industry expectations and regulatory frameworks such as NIST 800-171 and CMMC, with controls mapped across endpoint, email, network, and vulnerability management to support compliance and operational resilience.
External testing had reinforced that approach.
“From the external pentests, we thought we were King Kong… Then we started doing internal pentests, we realized we’re just running naked through the woods.”
The difference between external and internal testing was not incremental. It was fundamental.
To further test this assumption, the security lead introduced a realistic attacker starting point by injecting valid credentials into the environment and rerunning the assessment.
What followed was not a slow progression of isolated findings, but a rapid expansion of access across the domain.
Figure 3: Starting from a credentialed foothold, NodeZero mapped a full attack path through Active Directory, including service discovery, certificate abuse, and privilege escalation to domain admin.
The test demonstrated how quickly access could expand once an attacker was inside. Services were discovered, credentials were reused and elevated, and domain-level access was achieved through a sequence of legitimate, but exploitable, configurations.
Externally, the environment appeared hardened. Internally, attack paths emerged that had never been exercised. Weaknesses that were low priority on their own became critical when chained together. Credential exposure expanded access in ways that traditional testing had not revealed.
“All their patch management was up to date… it was just vulnerabilities that had never been added to the patch tools.”
The issue was not a lack of controls or effort, but a lack of visibility into how those controls performed when tested as a complete attack sequence.
Mitigation: Controls Validation
One of the most important findings was not what was missing, but what was already in place.
NodeZero identified endpoint detection across a significant portion of the environment, including multiple EDR solutions.
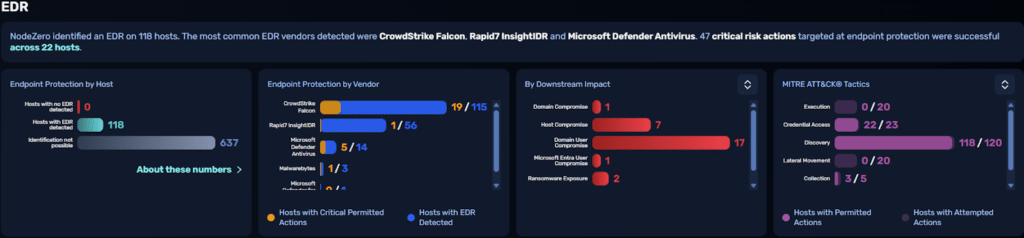
Figure 4: NodeZero identified multiple EDR solutions across 118 hosts, including CrowdStrike, Rapid7, and Microsoft Defender, while still successfully executing critical attack actions on protected systems.
The volume of EDR alerts reflected real activity, but this view made something else clear: critical attacker actions were still succeeding across protected hosts.
In total, 47 critical risk actions targeting endpoint protection were successfully executed across 22 hosts.
Detection was present across the environment, with coverage spanning multiple EDR solutions and alerts generated throughout the test, yet critical attacker actions still succeeded.
Credential dumping, lateral movement, and data access were achieved in multiple locations, including hosts with active protection. Some actions were blocked. Others were permitted. The outcome was not binary.
This is where many security programs struggle.
Controls are evaluated in isolation. Alerts are reviewed individually. What is rarely tested is how those controls behave across a full attack path.
The result is a gap between detection and outcome.
Mitigation: Threat Context
For an organization operating in the defense industrial base, understanding exposure is not just about internal risk. It is about adversary relevance.
NodeZero’s Threat Actor Intelligence mapped the observed weaknesses and impacts to known adversary tradecraft associated with Iranian threat groups.
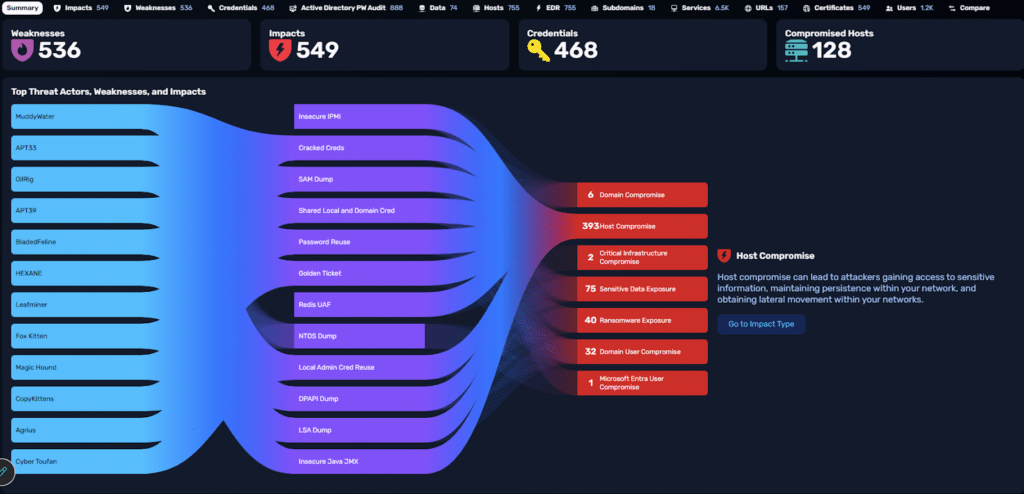
Figure 5: Threat Actor Intelligence mapping weaknesses and impacts to Iranian threat actors including MuddyWater, APT33, APT39, BladedFeline, and Agrius.
The techniques used in the test aligned with patterns observed in real-world campaigns targeting similar environments. Credential access, password reuse, and domain escalation are not edge cases. They are common entry points for persistent access and lateral movement.
This reframed the findings in a more operational context.
The issue was not just that compromise was possible.
It was that the path to compromise reflected how real adversaries operate.
Remediation
Once the attack paths were understood, remediation became more targeted.
Instead of working through long lists of vulnerabilities, the security team focused on breaking the connections that enabled compromise. The priority was clear: eliminate the weaknesses that allowed credentials to be captured and reused, and disrupt the paths that enabled lateral movement.
The impact of that approach was immediately measurable.
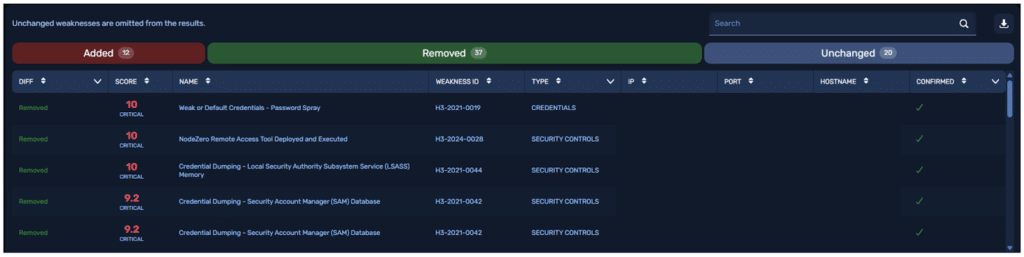
Figure 6: Targeted remediation removed high-risk weaknesses, including credential abuse and lateral movement techniques, with results validated through retesting.
Weaknesses tied to password spraying, credential dumping, and unauthorized remote access were removed. Retesting confirmed that previously viable attack paths no longer succeeded.
This shifted remediation from volume-based activity to outcome-driven validation.
Conclusion
The organization did not lack tools, processes, or expertise.
Their controls were in place. Their external testing was consistent. Their security program met expectations.
What was missing was validation under real conditions.
External testing showed a clean perimeter. Internal testing showed how quickly that changed once an attacker gained access.
Detection was present, but detection alone did not prevent compromise.
The attack path was not theoretical. It was executed. And it aligned with adversary behavior relevant to the organization’s role in the defense industrial base.
“The unknown unknowns will get you every time.”
That is the gap.
Not visibility into alerts.
Not visibility into vulnerabilities.
Visibility into outcome.
And until that is tested, security remains an assumption, not a validated outcome.