CVE-2026-3324
ManageEngine Log360 Authentication Bypass Vulnerability
ManageEngine has disclosed CVE-2026-3324, a high-severity authentication bypass vulnerability affecting Log360 builds 13000 through 13013. According to the vendor, the issue affects exposed V1 APIs and can result in authorization checks being bypassed, potentially enabling unauthorized access to data and operations. ManageEngine fixed the issue in build 13017, released on March 10, 2026.
Technical Details
CVE-2026-3324 describes an authentication bypass vulnerability affecting exposed V1 APIs in ManageEngine Log360. ManageEngine states that affected versions are builds 13000 through 13013, and that successful exploitation could allow unauthorized access to data and operations by bypassing authorization checks. The issue is resolved in build 13017.
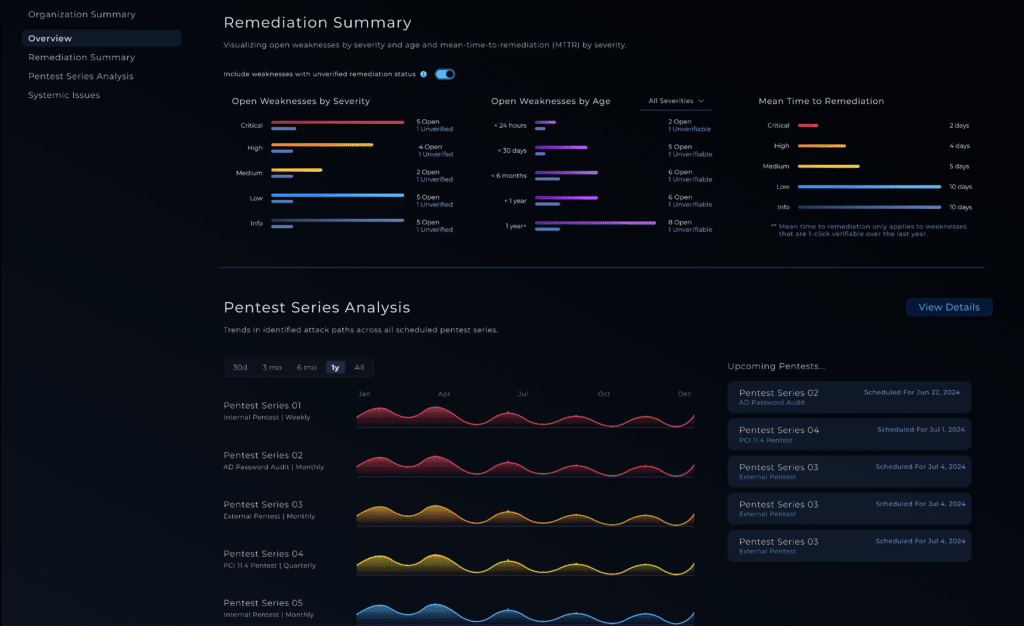
NodeZero® Proactive Security Platform — Rapid Response
Horizon3.ai has prepared Rapid Response messaging for CVE-2026-3324 in the GTM guide you shared.
- Run the Rapid Response test: Horizon3.ai customers can launch the test from the customer portal to determine whether exposed Log360 systems are vulnerable.
- Patch immediately: Upgrade affected Log360 instances from builds 13000 through 13013 to build 13017 or later. ManageEngine’s service pack page says users on builds 13000 through 13016 should install Service Pack 13.1.1, which corresponds to build 13017.
- Re-run the Rapid Response test: Validate that the upgrade removed exploitability and confirm the exposure has been closed.
Affected versions & patch
- Affected: ManageEngine Log360 builds 13000 through 13013.
- Fixed: Build 13017.
- Fixed on: March 10, 2026.
- Patch guidance: Update to build 13017 or later using ManageEngine’s service pack process.
Timeline
- March 10, 2026: ManageEngine released Log360 build 13017.
- April 17, 2026: ManageEngine published the public Log360 advisory for CVE-2026-3324 describing the affected versions, impact, and fix.