CVE-2026-21643
Fortinet FortiClient EMS SQL Injection Vulnerability
Fortinet FortiClient EMS contains a critical SQL injection vulnerability that may allow an unauthenticated attacker to execute unauthorized code or commands via specifically crafted HTTP requests. The vulnerability affects FortiClient EMS 7.4.4, carries a CVSS v3.1 score of 9.8, and Fortinet says it has been observed to be exploited in the wild.
Technical Details
CVE-2026-21643 is a CWE-89 SQL injection vulnerability in the FortiClient EMS administrative interface. Fortinet states that the flaw may allow an unauthenticated attacker to execute unauthorized code or commands through specifically crafted HTTP requests. Fortinet lists the issue as Critical, identifies the component as the GUI, and says the attack type is unauthenticated. The affected version in the 7.4 branch is 7.4.4. FortiClient EMS 7.2 and 8.0 are listed as not affected.
This matters because FortiClient EMS is a centralized endpoint management platform. A successful compromise of that management layer can create a high-impact foothold for an attacker. The vendor advisory supports the clearest public claim here: the vulnerability can lead to unauthorized code or command execution on the EMS server. Public reporting on March 30, 2026 said attackers had already begun exploiting the flaw in the wild.
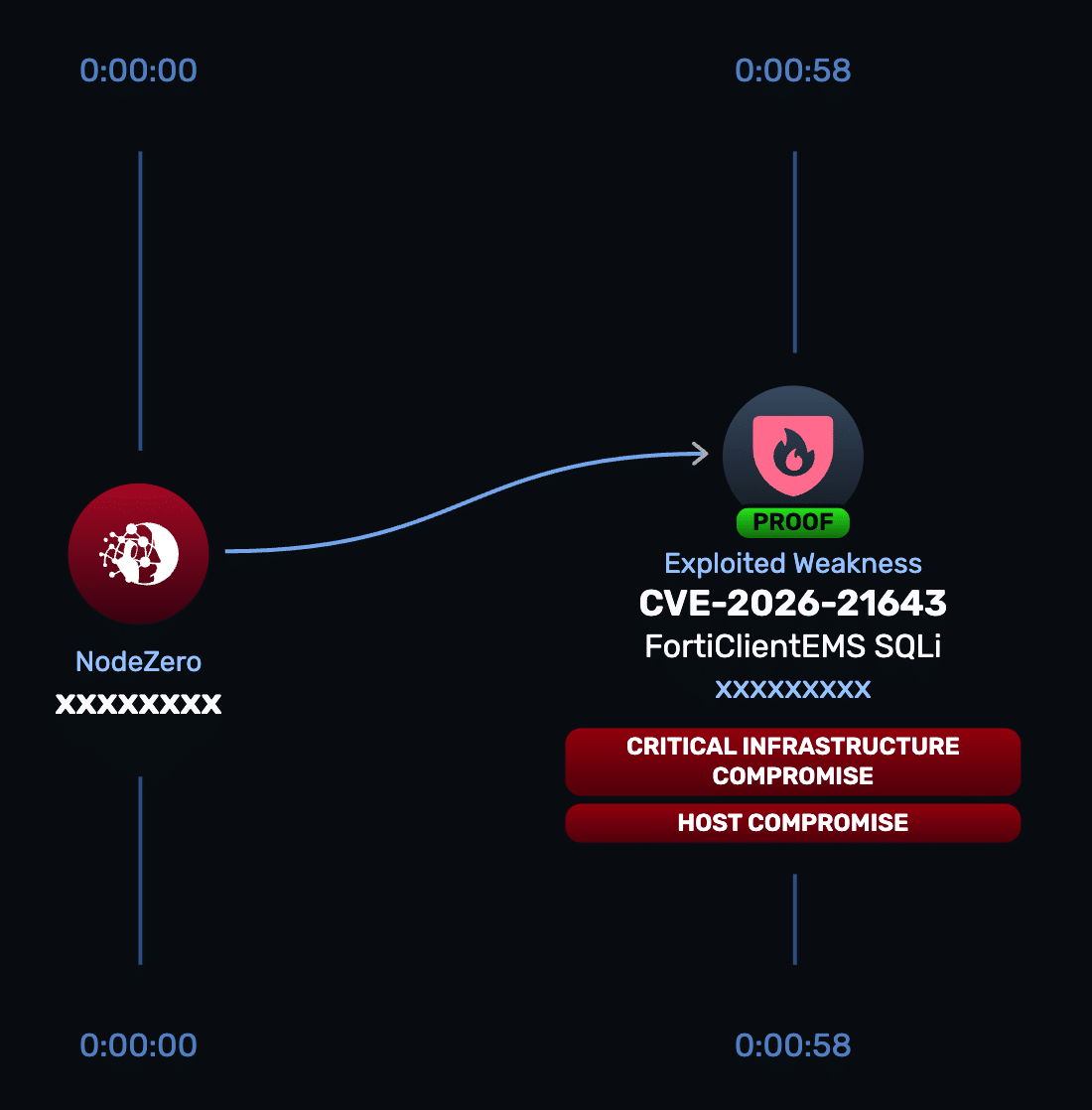
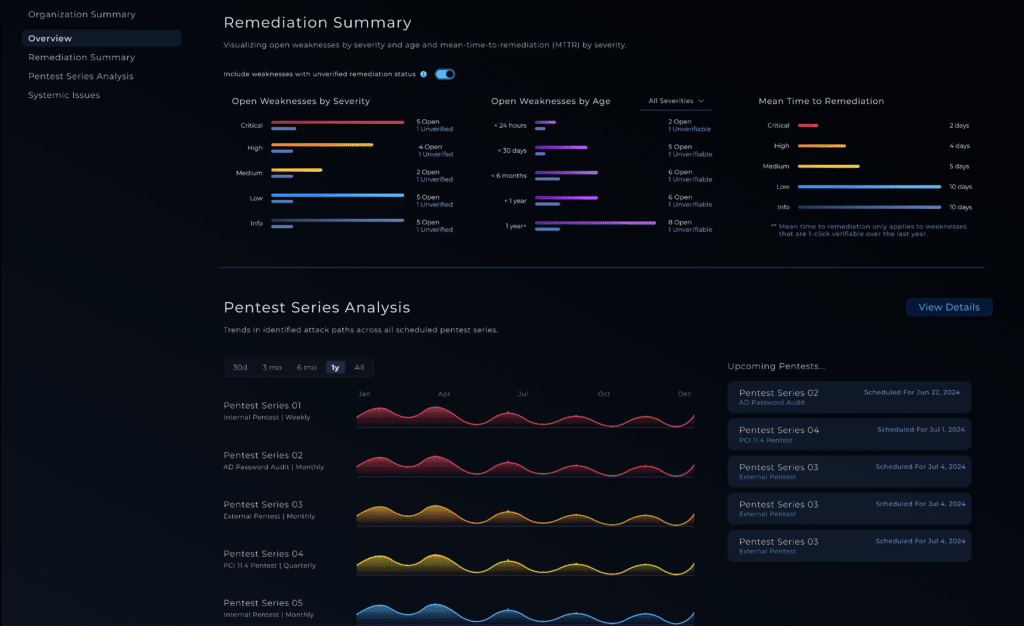
NodeZero® Proactive Security Platform — Rapid Response
When a critical advisory drops, the first question is simple: does this actually expose my environment?
NodeZero Rapid Response helps answer that directly by safely validating exploitability on-demand.
- Run the Rapid Response test: Horizon3.ai customers can launch the test from the portal to determine whether FortiClient EMS is exploitable in their environment.
- Patch immediately: Fortinet says customers running FortiClient EMS 7.4.4 should upgrade to 7.4.5 or above.
- Restrict access while patching: If patching cannot happen immediately, restrict access to the EMS administrative interface and related services to trusted hosts and networks only.
- Re-run the Rapid Response test: After patching or restricting access, re-test to confirm the exposure has been removed.
Indicators of Compromise
Fortinet’s advisory for CVE-2026-21643 does not provide a dedicated IOC section with attacker IPs, hashes, filenames, or command strings. Public reporting confirms exploitation activity, but the vendor advisory does not publish concrete hunting artifacts for this CVE. Because of that, this section should either remain omitted or stay minimal rather than inventing indicators that are not in the source material.
Affected versions & patch
- Affected: FortiClient EMS 7.4.4.
- Not affected: FortiClient EMS 7.2 and 8.0.
- Patch: Upgrade to FortiClient EMS 7.4.5 or above.
Timeline
- February 6, 2026 – Fortinet published advisory FG-IR-25-1142.
- March 30, 2026 – BleepingComputer reported active exploitation, citing Defused.
- April 13, 2026 – CISA’s advisories page shows an alert titled “CISA Adds Seven Known Exploited Vulnerabilities to Catalog,” and secondary reporting states CVE-2026-21643 was among the additions.