Security Practitioner
SEARCH
CATEGORIES
TAGS
The 2026 Buyer’s Guide to Penetration Testing
May 20, 2026
The 2026 Buyer’s Guide to Penetration Testing explains how security leaders are reevaluating pentesting based on exploitability, validation, and real-world attack paths.
From Point-in-Time Testing to Continuous Security Validation
May 18, 2026
Learn how Mid Devon District Council moved beyond annual pentests to continuously validate exploitable risk, strengthen identity security, and accelerate remediation with autonomous pentesting.
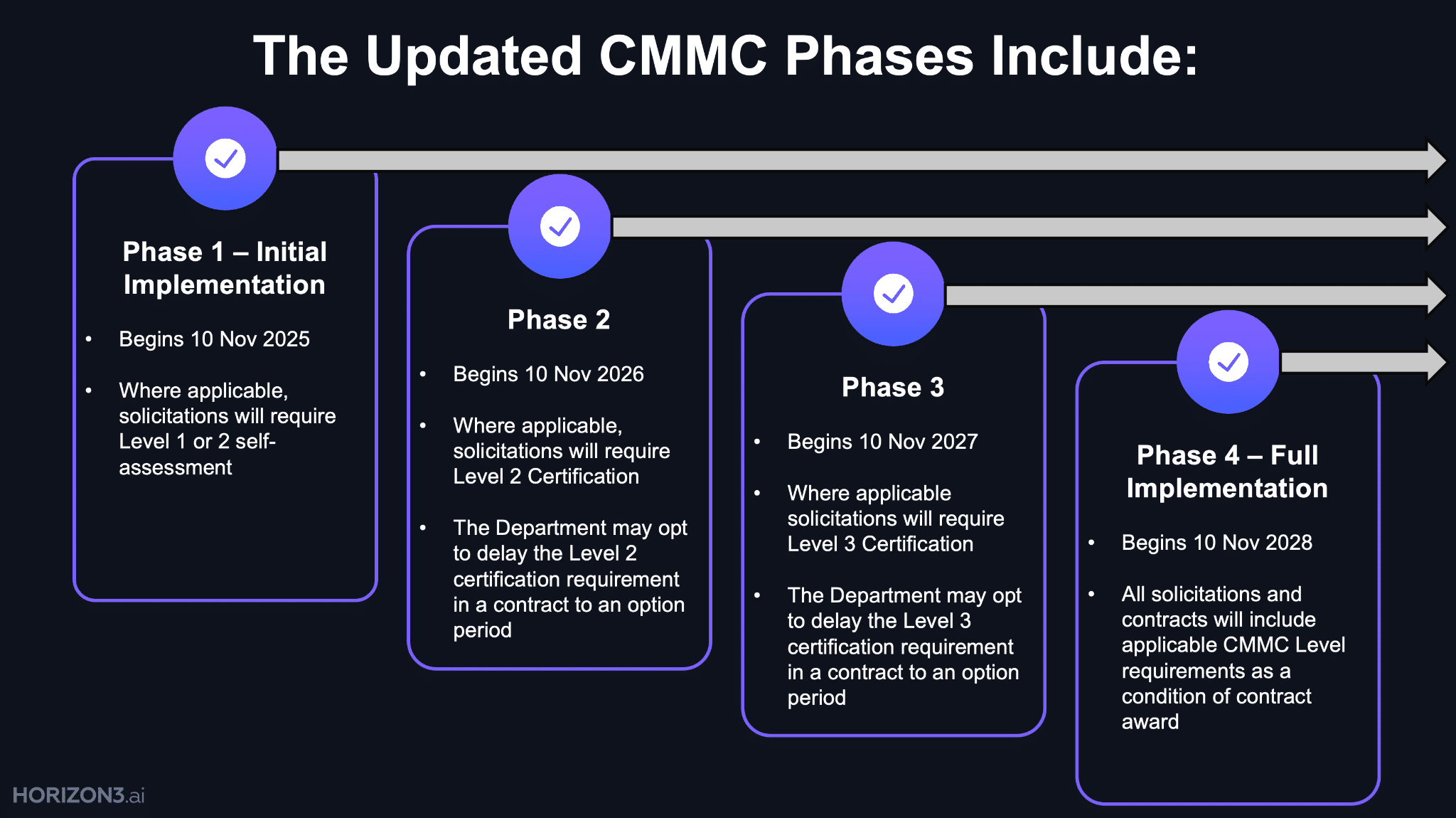
Strengthen Supply Chain Security for CMMC
May 18, 2026
This whitepaper explains how organizations can move beyond CMMC compliance to continuously validate real-world security across the supply chain.
You’re Only as Secure as Your Last Evaluation
May 18, 2026
CMMC is shifting cybersecurity from periodic compliance to continuous validation across the Defense Industrial Base supply chain.
Autonomous AI Cyber Defense You Can Trust in Production
May 6, 2026
New research reveals how to make AI-powered cyber defense safe, stable, and reliable for real-world deployment.
Unifying SOC and ITSM
May 5, 2026
A leadership guide to aligning SOC and ITSM teams using evidence-driven cyber risk management and real-world validation.
Project Glasswing & NodeZero® factsheet
April 28, 2026
See how Glasswing and NodeZero combine to identify vulnerabilities and validate which ones can actually be exploited.
Mythos in Practice: Attack Paths, Exploitability, and What Actually Matters Most
April 22, 2026
Mythos shows how vulnerabilities become real risk—by chaining into attack paths that lead to impact.
Mythos Didn’t Break Cybersecurity. It Exposed What Was Already Broken.
April 17, 2026
Mythos shows that finding vulnerabilities isn’t the problem—understanding exploitability and impact is what security teams are missing.
Incident Response Remediation: How to Eliminate Attack Paths After a Breach
April 8, 2026
Digital threat monitoring shows threats and exposure—but not whether attackers can exploit your environment. Here’s what matters next.