Mythos didn't break cybersecurity.
It exposed what was already broken.
Finding vulnerabilities was never the hard part. The gap between discovery and real-world impact is collapsing, shifting the focus to rapidly determining which ones can actually be exploited.
Reactions to Mythos have been predictable.
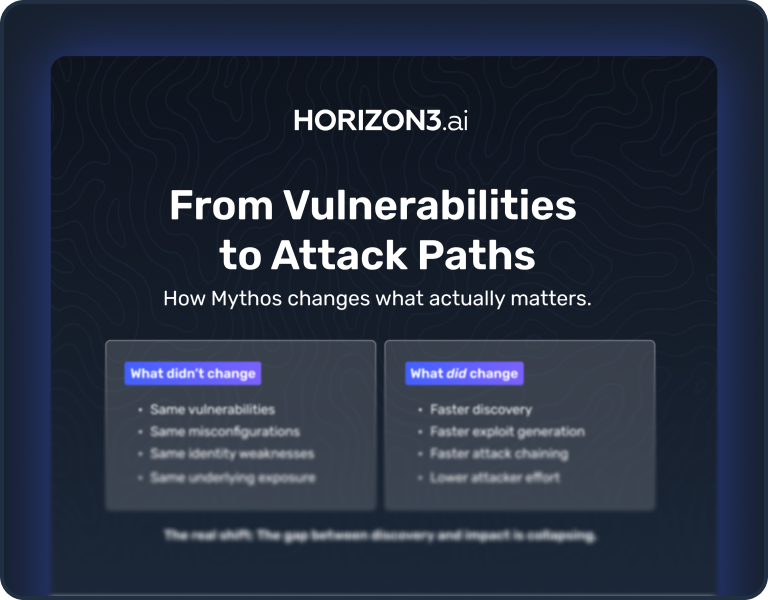
The reality is many are missing the point. Mythos doesn’t introduce new classes of vulnerabilities or change how attacks work.
It reduces the effort required to find, validate, and chain weaknesses together. The underlying conditions haven’t changed. What’s changed is how quickly they can be exposed.
What actually changed.
The shift Mythos drives is defined by the total collapse of the gap between identifying a flaw and achieving a real-world breach, specifically through these three key advancements:
Accelerated Vulnerability Weaponization
Mythos compresses the time from discovery to exploit generation, turning raw findings into usable attack capabilities.
Lowering the Barrier to Entry
By automating how weaknesses are chained, Mythos enables meaningful impact without requiring specialized expertise.
The Compression of the Attack Path
Mythos compresses the path from initial access to lateral movement, reducing the time to reach high-value assets to near zero.
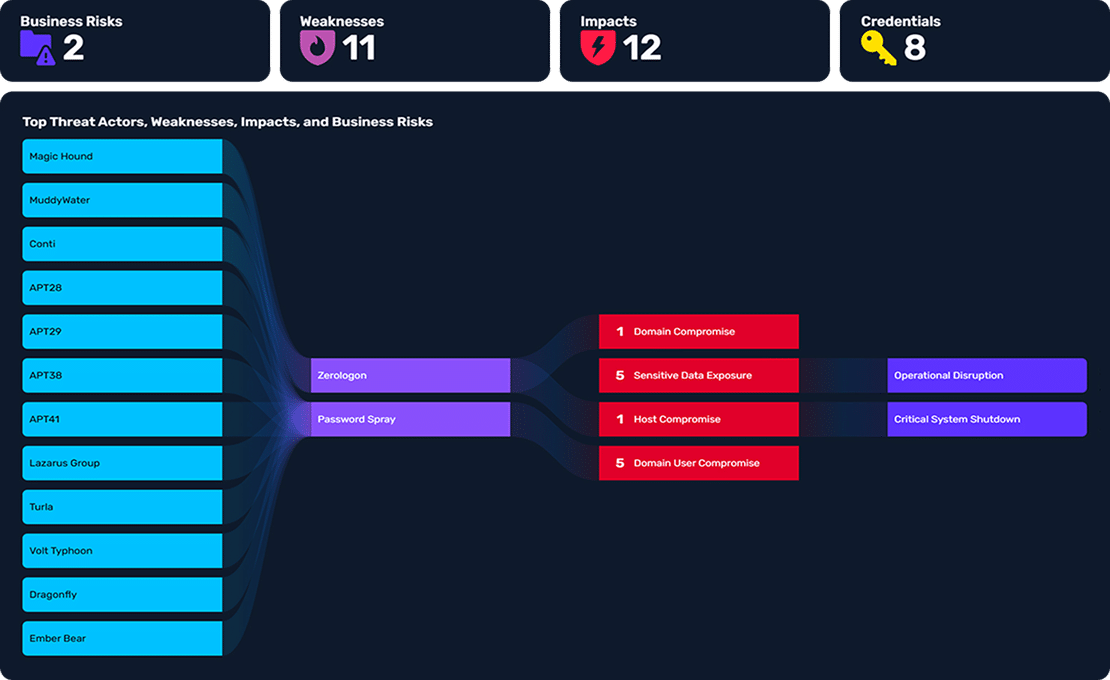
Attackers don't exploit vulnerabilities.
They chain together weaknesses to create exploit paths. Most environments already contain the pieces. You can’t prioritize what you don’t test.
Nothing changed — except how fast it all happens. And that changes everything.
What does Mythos actually mean
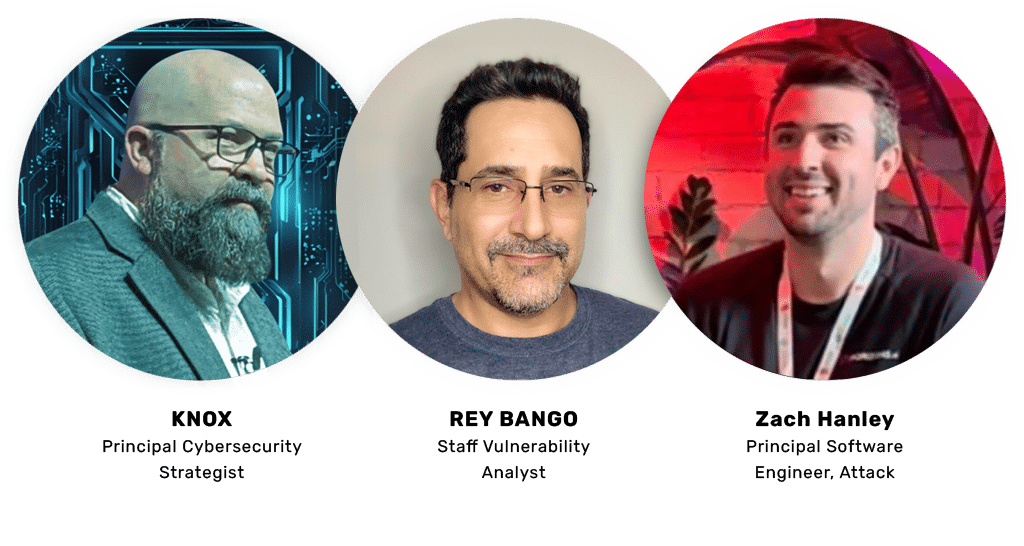
We are moving past the scattered narratives to take a definitive, grounded stance on what Mythos changes and what it doesn’t. In this strategic briefing, our panel will explore the shifting threat landscape without giving in to fear-driven marketecture.
Panel topics include:
- The New Economics of Exploitation
- Cyber Ranges vs. Production Realities
- The “Assume Breach” Imperative
What matters now
The conversation has to change. What matters now is not how many vulnerabilities exist, but what can actually be exploited, how weaknesses connect, and how quickly those paths can be used to reach real impact.
NodeZero®, the world’s best AI Hacker, was built for this shift. Not to generate more findings, but to solve the problems that actually matter.
Mythos Resources
Real AI-driven attacks, run safely in production.
Horizon3.ai’s NodeZero® enables teams to validate what attackers can actually exploit in their environment. The most reliable way to understand risk is to see how attacks actually unfold.