Resource Center
Welcome to our cybersecurity resource center where we uncover how malicious actors exploit weaknesses in systems, while going beyond the technical aspects and examining real-world perspectives across various industries.
LATEST VULNERABILITIES
Fortinet FortiSIEM Arbitrary File Write Remote Code Execution Vulnerability
Read More →WEBINAR REPLAY
SEARCH
CATEGORIES
TAGS
SEARCH
CATEGORIES
TAGS
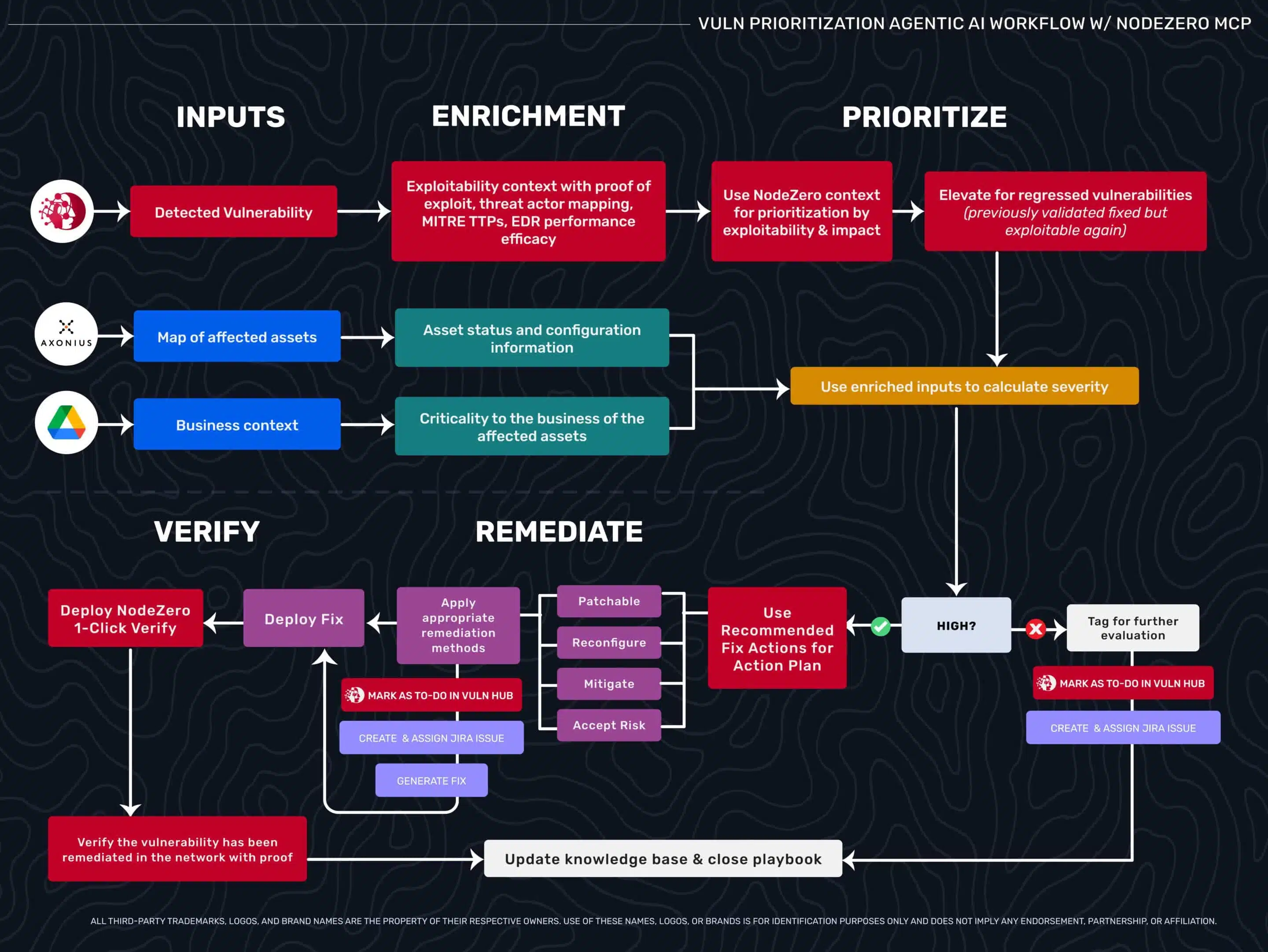
Beyond Triage: How Exploitability Data Transforms Agentic Security Workflows
Security teams drown in critical CVEs that don’t matter while missing medium flaws that lead to domain admin. This blog explores how exploitability data—validated through autonomous pentesting—enables agentic AI workflows to move beyond triage, prioritize what’s truly exploitable, and automate verification with confidence.
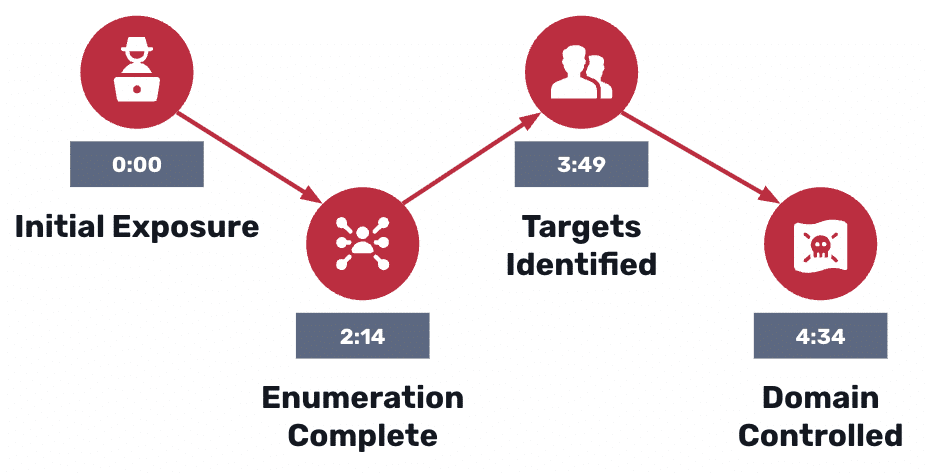
The Quiet Attack Path
October 21, 2025
Attackers turn native Active Directory features into a low-noise, high-impact playbook: stealthy enumeration, Kerberoasting, and AS-REP roasting can produce crackable credentials and clear paths to domain admin in minutes. This post walks through the first 15 minutes of an AD intrusion, why traditional SIEM/EDR struggles to detect it, and what defenders must catch early to…
From Patch Tuesday to Pentest Wednesday®: How a Global Chemical Manufacturer De-Risked a $2B Merger
October 15, 2025
When a $2B merger put a global chemical manufacturer’s security to the test, NodeZero® exposed critical identity risks and domain compromise paths in just 35 minutes. What began as a pilot evolved into a global Pentest Wednesday® program—turning vulnerability data into proof of resilience across 20 sites and thousands of endpoints.
What is ITDR and Why Active Directory (AD) Tripwires Make It Real
Annual pentesting leaves blind spots. Learn why modern threats demand frequent or continuous pentesting to stay ahead of attackers.
How Often Should You Pentest?
Annual pentesting leaves blind spots. Learn why modern threats demand frequent or continuous pentesting to stay ahead of attackers.
From Patch Tuesday to Pentest Wednesday®: Proof That Reshaped Security for a Gaming Operator
September 17, 2025
A U.S. casino's first pentest uncovers 756 weaknesses & 143 attack paths, sparking a new, proof-driven approach to security.
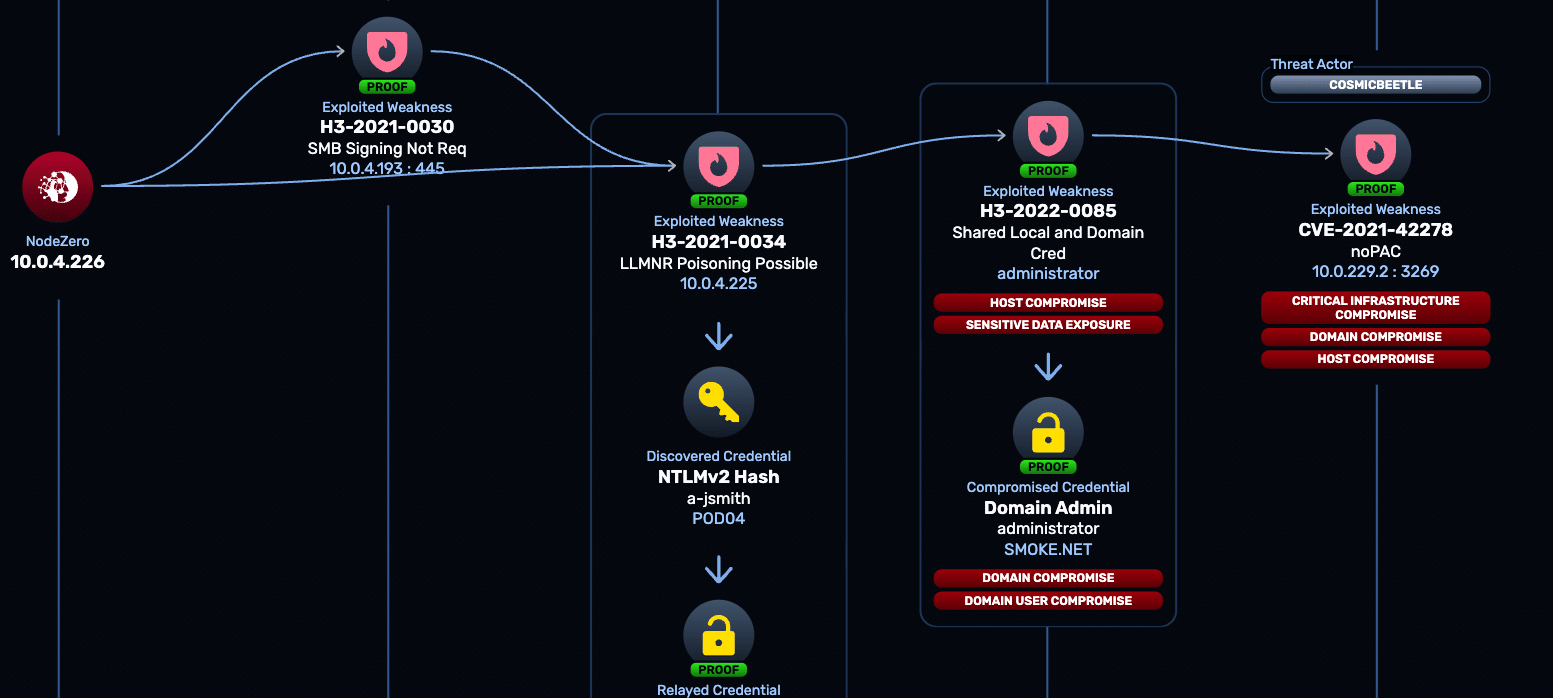
Threat Actor Intelligence: Known Threats, Known Weaknesses, Known Outcomes
September 12, 2025
Awareness doesn’t equal defense. Threat Actor Intelligence helps you go beyond the headline: “Are these attackers using techniques that would actually work in our environment?”
From Patch Tuesday to Pentest Wednesday®: Proof That Redefined Security for a Large Insurer
September 10, 2025
The simple truth is that supply chain security depends on validation, not paperwork. Pentest Wednesday is about moving from forms and annual tests to continuous testing and measurable risk reduction, replacing paperwork with proof.
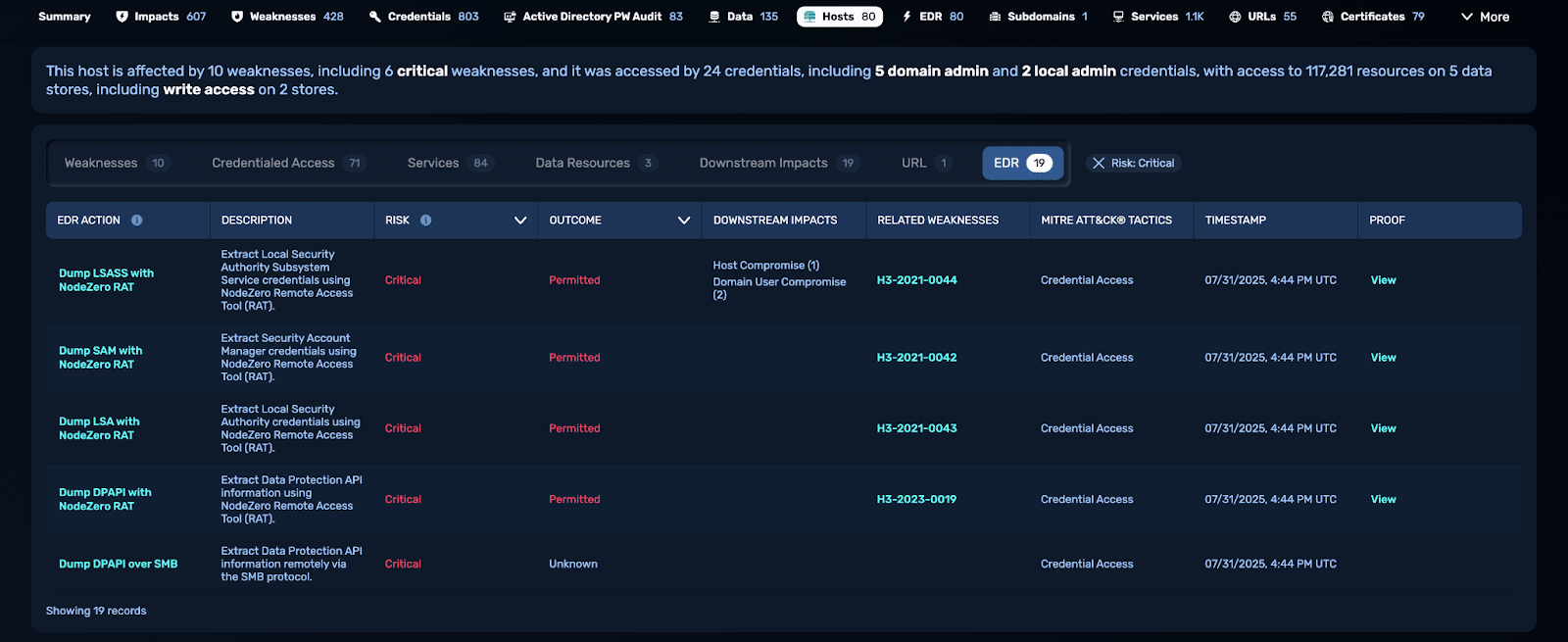
Endpoint Security Effectiveness: From Assumption to Proof
EDR and XDR platforms are positioned as the backbone of endpoint protection. They promise to detect, block, and contain threats before attackers can gain a foothold. Yet many organizations are left asking the same questions: Where is our EDR deployed? Is it configured properly? Could something be slipping through? The uncomfortable truth is that most…