Resource Center
Welcome to our cybersecurity resource center where we uncover how malicious actors exploit weaknesses in systems, while going beyond the technical aspects and examining real-world perspectives across various industries.
LATEST VULNERABILITIES
CVE-2026-0257 is a critical authentication bypass vulnerability in Palo Alto Networks PAN-OS GlobalProtect that allows unauthorized VPN access and is actively exploited in the wild.
Read More →CVE-2026-44825 is a hardcoded credentials vulnerability affecting Apache Solr Basic Authentication setup workflows. The flaw may allow attackers to gain administrative access to vulnerable SolrCloud deployments.
Read More →WEBINAR REPLAY
SEARCH
CATEGORIES
TAGS
SEARCH
CATEGORIES
TAGS
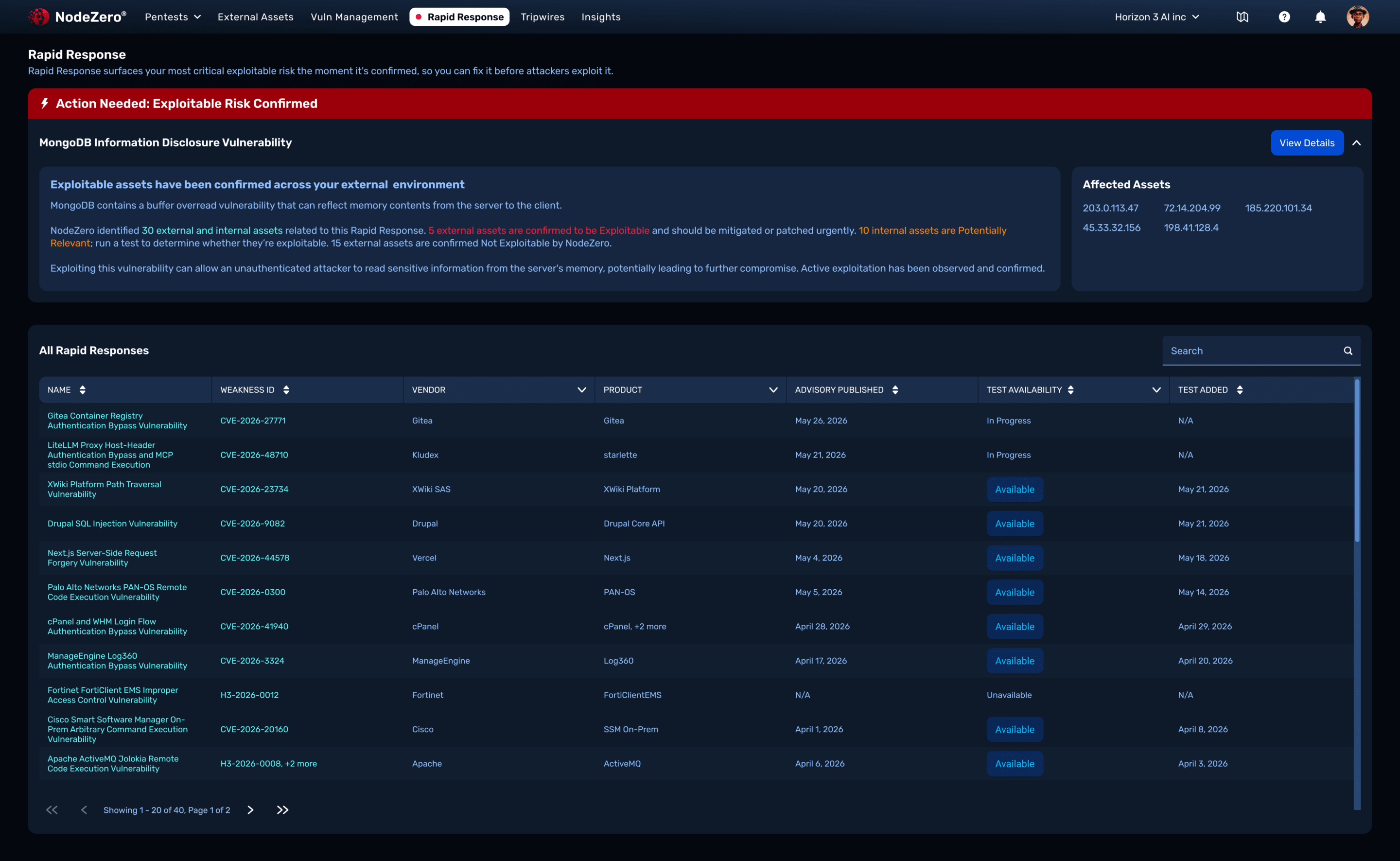
The Exploit Window Is Shrinking. Most Security Workflows Are Not.
June 1, 2026
AI is accelerating vulnerability discovery and attacker weaponization. Learn how Rapid Response helps organizations validate exposure, reduce uncertainty, and close the exploit window faster.
Rapid Response
May 29, 2026
Rapid Response enables organizations to quickly determine which emerging vulnerabilities create real exploitability risk, prioritize remediation, and verify fixes before attackers operationalize threats.
AI Has Ideas. sqlmap Has Receipts.
May 29, 2026
AI can identify potential SQL injection opportunities, but deterministic validation is what builds trust. Learn how NodeZero® combines LLM-guided discovery with sqlmap to deliver high-confidence findings.
Third-Party Risk Management
May 27, 2026
NodeZero for TPRM: NodeZero proactively secures your supply chain by replacing assumptions with proof. It empowers you to find, fix, and validate third-party risks before they disrupt your business.
The 2026 Buyer’s Guide to Penetration Testing
May 20, 2026
The 2026 Buyer’s Guide to Penetration Testing explains how security leaders are reevaluating pentesting based on exploitability, validation, and real-world attack paths.
From Point-in-Time Testing to Continuous Security Validation
May 18, 2026
Learn how Mid Devon District Council moved beyond annual pentests to continuously validate exploitable risk, strengthen identity security, and accelerate remediation with autonomous pentesting.
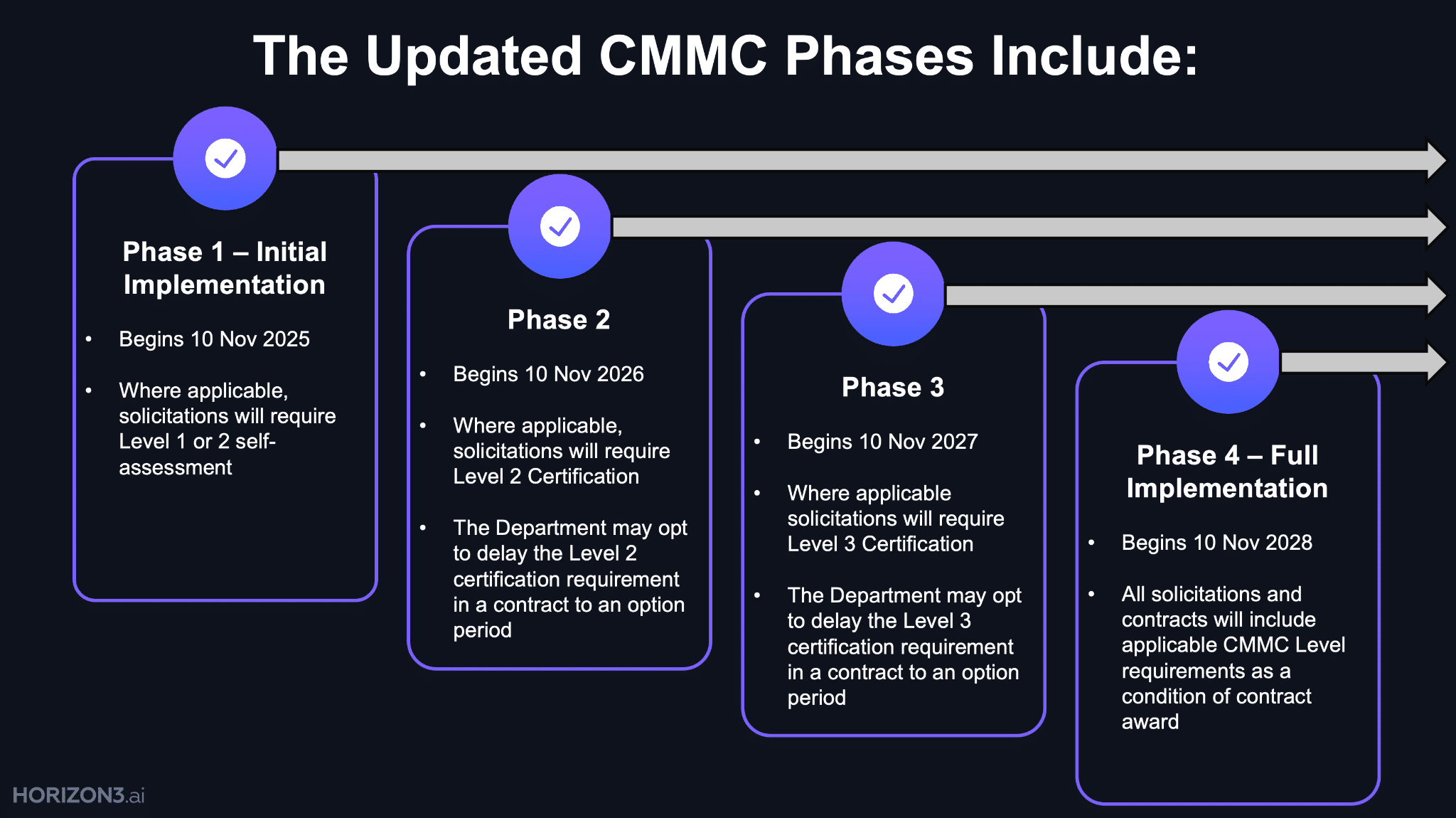
Strengthen Supply Chain Security for CMMC
May 18, 2026
This whitepaper explains how organizations can move beyond CMMC compliance to continuously validate real-world security across the supply chain.
You’re Only as Secure as Your Last Evaluation
May 18, 2026
CMMC is shifting cybersecurity from periodic compliance to continuous validation across the Defense Industrial Base supply chain.
From Patch Tuesday to Pentest Wednesday®: How a Software Provider Closed Unknown Paths to Cloud Compromise
May 13, 2026
A healthcare software provider uncovered hidden attack paths to AWS compromise and transformed security operations through continuous validation.
Autonomous AI Cyber Defense You Can Trust in Production
May 6, 2026
New research reveals how to make AI-powered cyber defense safe, stable, and reliable for real-world deployment.