Resource Center
Welcome to our cybersecurity resource center where we uncover how malicious actors exploit weaknesses in systems, while going beyond the technical aspects and examining real-world perspectives across various industries.
LATEST VULNERABILITIES
BeyondTrust Privileged Remote Access and Remote Support | Pre-Auth Remote Code Execution
Read More →SolarWinds Web Help Desk Deserialization Vulnerability | Active Exploitation
Read More →WEBINAR REPLAY
SEARCH
CATEGORIES
TAGS
SEARCH
CATEGORIES
TAGS
From Patch Tuesday to Pentest Wednesday®: Proof That Protects Healthcare
August 20, 2025
A Pentest Wednesday® Story Every security leader knows about Patch Tuesday. It’s the rhythm Microsoft set decades ago to deliver updates and fixes, and it quickly became a mainstay of IT and security operations. Teams plan change-windows around it. Vendors align updates to it. And for many organizations, Patch Tuesday has become the de facto…
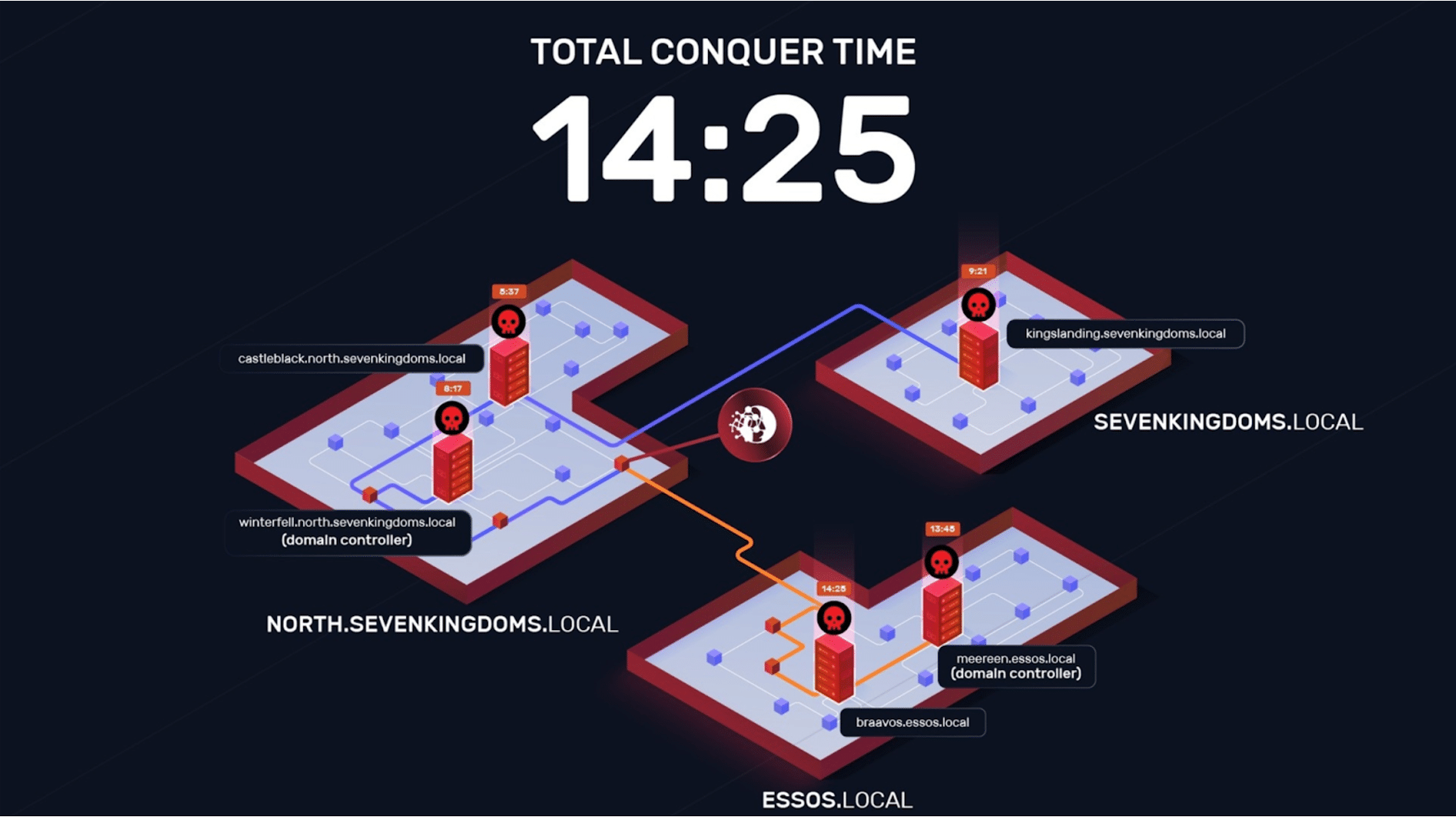
NodeZero® vs. GOAD: Technical Deep Dive
NodeZero autonomously compromised GOAD in 14 mins by exploiting common Active Directory misconfigurations.
Lessons Learned from 100k Pentests with Carahsoft
Combating Modern Cybersecurity Challenges with Offensive Security Principles Despite global cybersecurity spending projected to reach $212 billion in 2025, 84% of organizations still experienced breaches in the past year. This disconnect between investment and outcomes reveals fundamental flaws in traditional defensive approaches. Drawing from insights gained through over 100,000 autonomous penetration tests conducted across diverse…
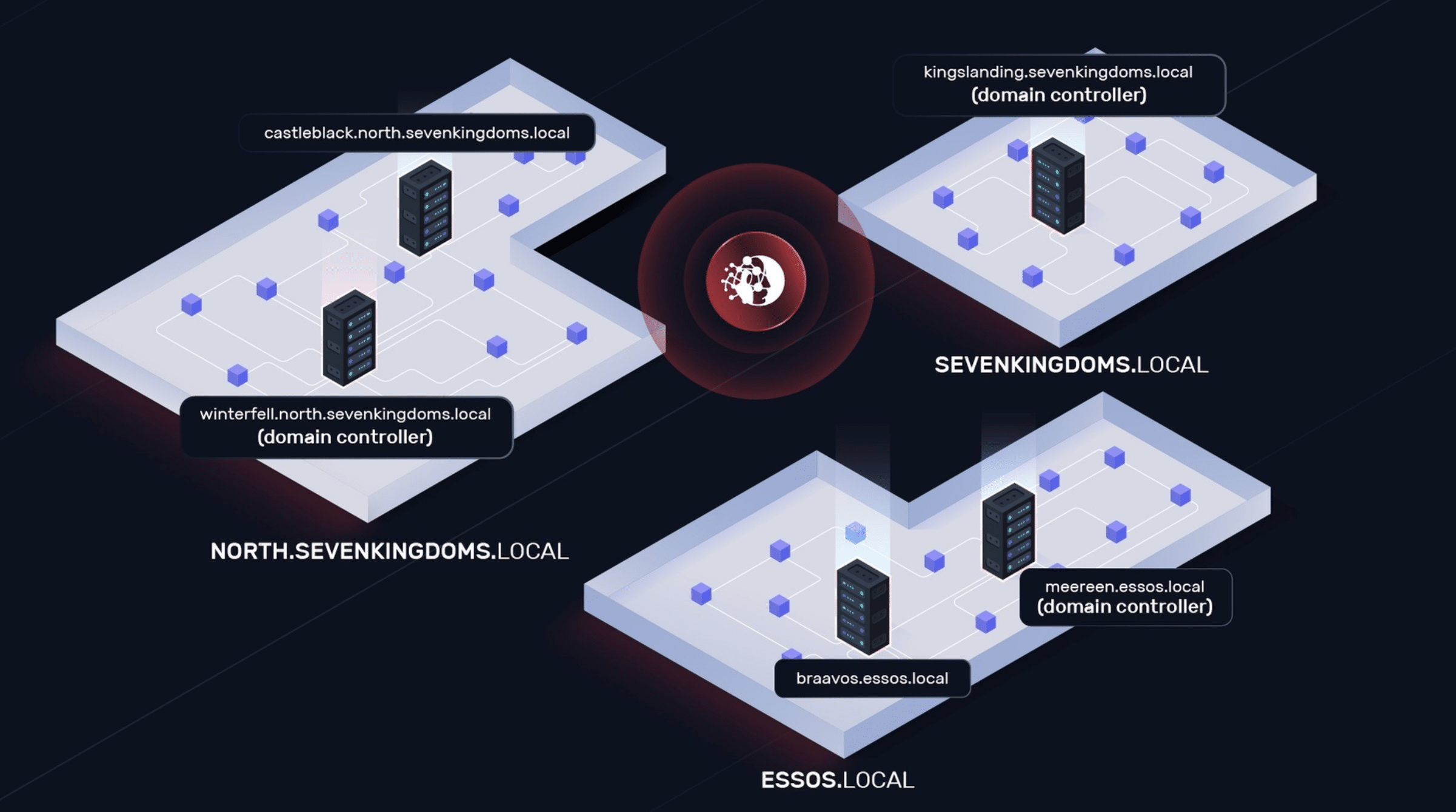
How to Run NodeZero® vs. GOAD
GOAD (Game Of Active Directory) is an intentionally vulnerable cyber range used by pentesters and defenders to explore common attack techniques in a Windows Active Directory environment. It's chock full of real-world misconfigurations and vulnerabilites, the type we see all the time in client environments. As such, it's a great way to understand the capabilities…
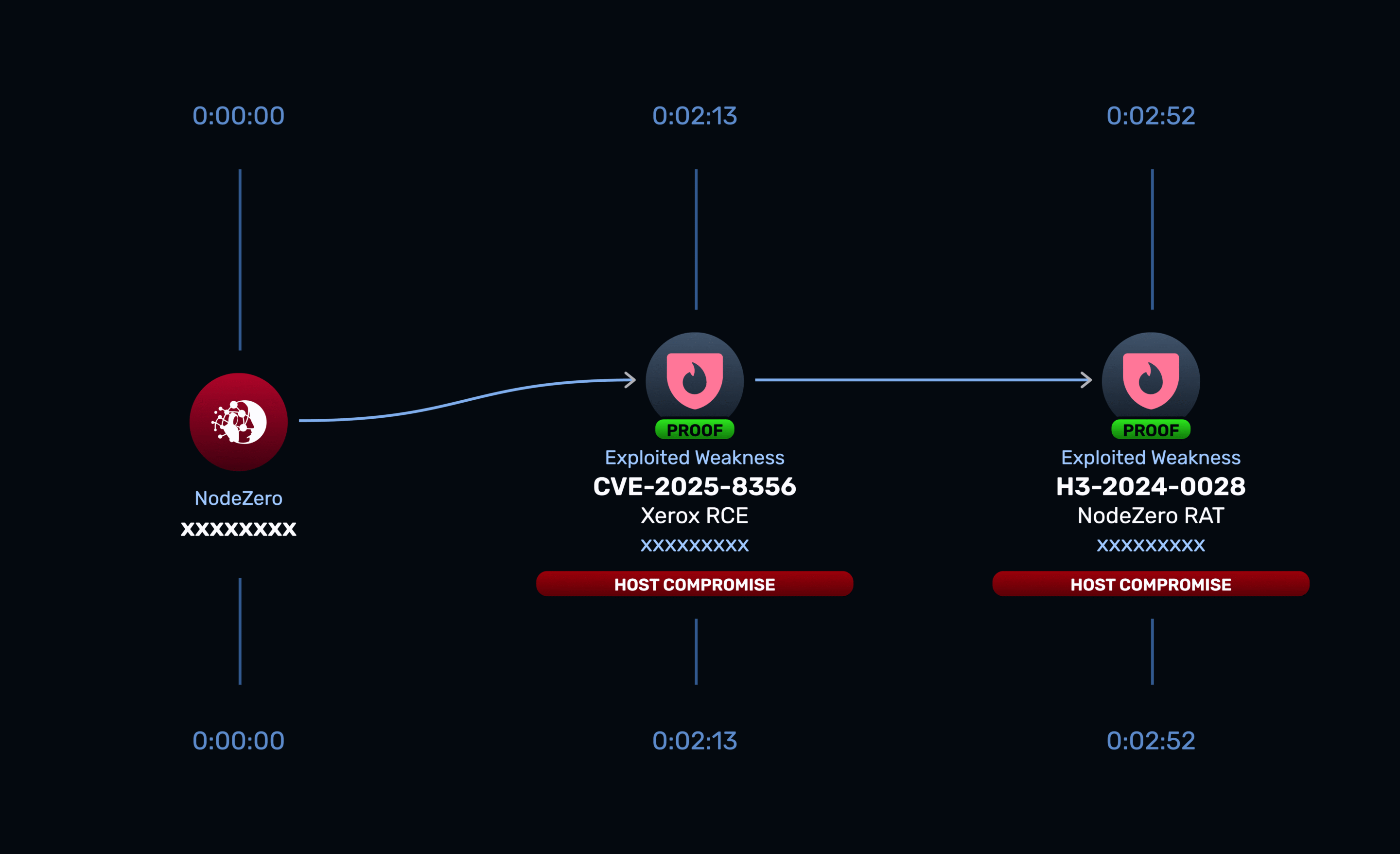
From Support Ticket to Zero Day
August 13, 2025
Examining a Critical Vulnerability in Xerox FreeFlow Core
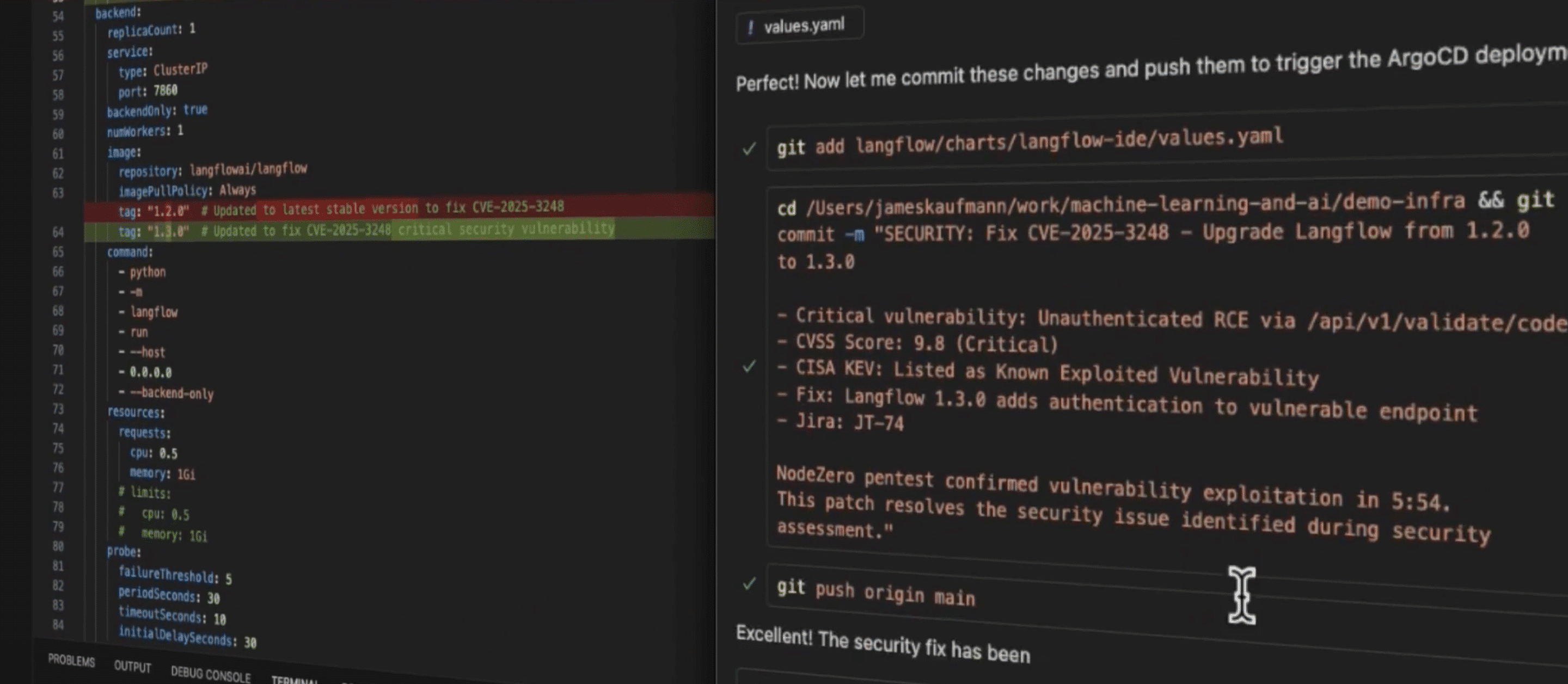
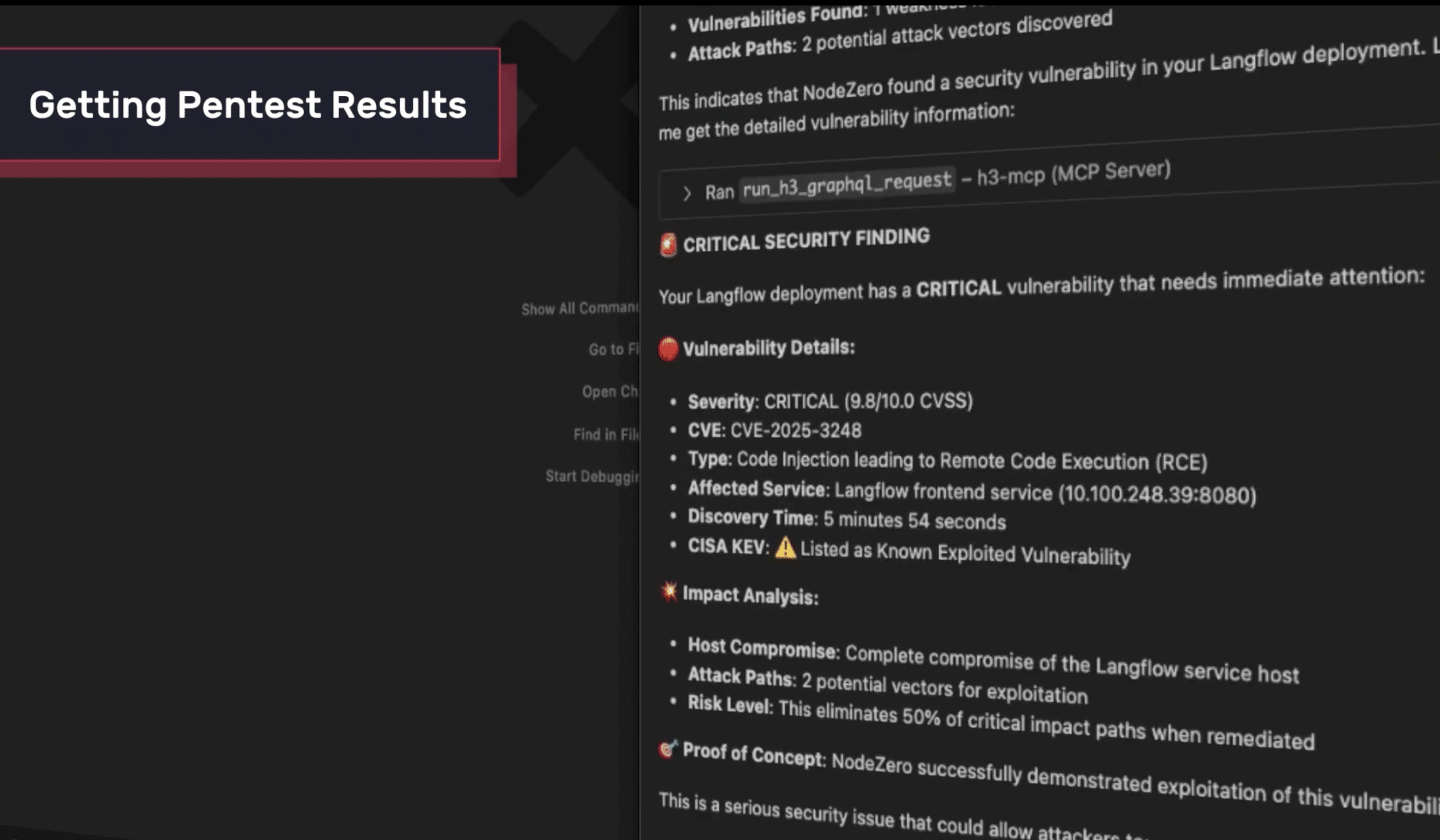
Supercharge Enterprise AI with the Attacker’s Perspective: Introducing the NodeZero® MCP Server
Enterprises are racing to harness AI to automate workflows, secure infrastructure, and accelerate decision-making. But here’s the uncomfortable truth: AI that doesn’t see your environment through an attacker’s eyes is operating blind.
Securing the NodeZero® MCP Server: Building a Safe, Agent-Ready Runtime for Enterprises
When we set out to build the first version of the NodeZero MCP Server, we had two guiding principles: Most Model Context Protocol (MCP) servers today are overpowered and underdefended. They often: We didn’t build ours that way. The NodeZero MCP Server is a constrained, API-native runtime designed to give agents safe, structured access to…
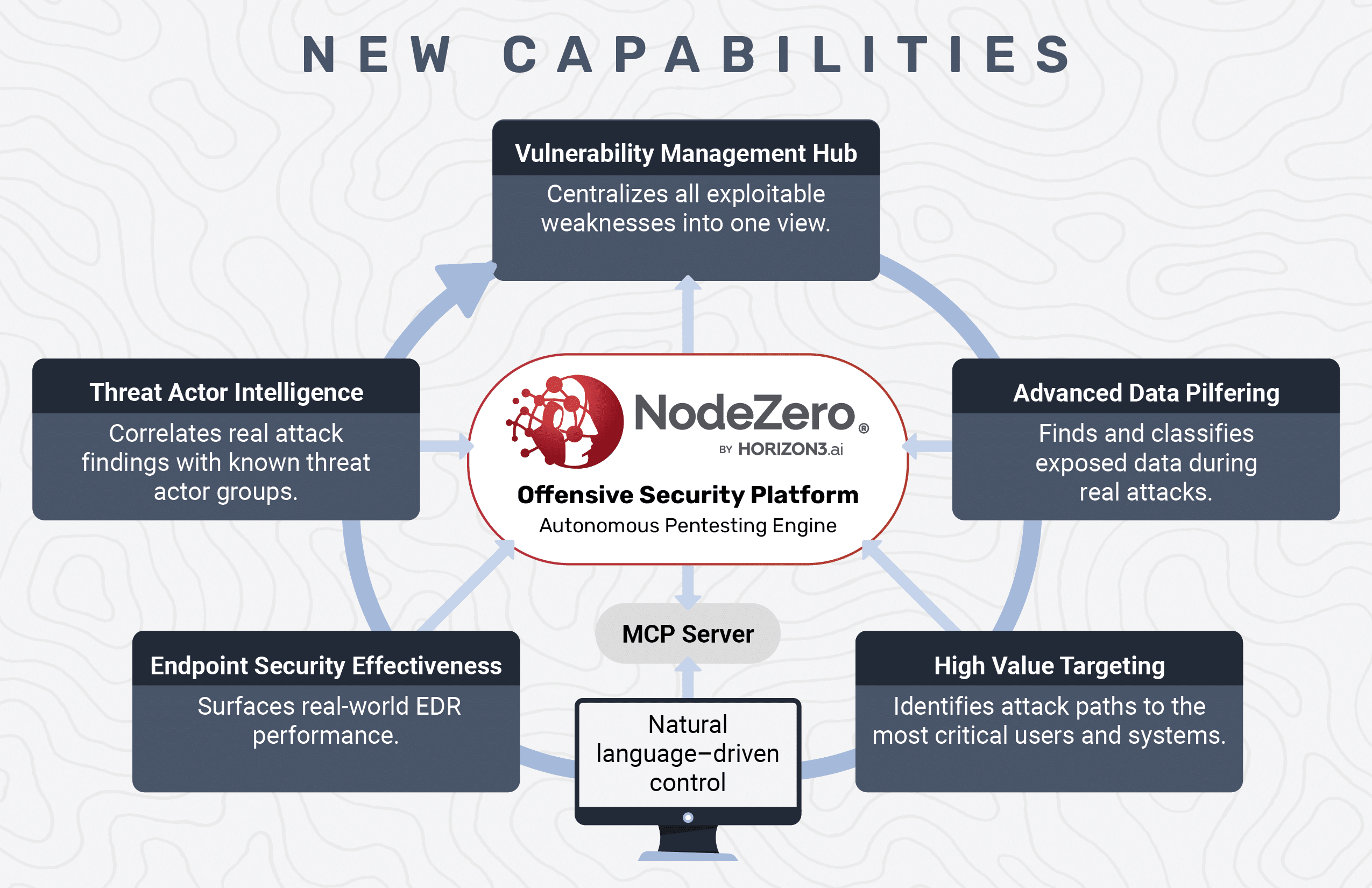
Fix What Matters Most: Six New NodeZero® Capabilities That Redefine Risk-Based Vulnerability Management
Vulnerability management started with scanning — identify assets, fingerprint software, and match scan findings to known CVEs. Then came “risk-based” approaches that promised smarter prioritization. But in practice, most programs still just patch what scores the highest. Risk is inferred, not proven. Fixes are assumed to work. And security teams are left guessing what actually…
Proof, Not Promises: Redefining Cybersecurity for the Defense Industrial Base
The Defense Industrial Base (DIB) is the backbone of national security—and is a high-value target for advanced cyber adversaries exploiting weaknesses across the supply chain. In this joint keynote, Snehal Antani, CEO of Horizon3.ai and special guest Bailey Bickley, Chief of DIB Defense at the NSA Cybersecurity Collaboration Center reveal how the NSA’s Continuous Autonomous…
Vulnerability Management Is Broken: There is a Better Way
July 28, 2025
Scanning and patching aren't enough. Learn the critical difference between being vulnerable and being exploitable—and why it's the key to preventing real-world breaches.