CVE-2025-32756
Fortinet Multiple Products Stack-Based Buffer Overflow Vulnerability
A critical vulnerability, CVE-2025-32756, has been identified in various Fortinet products, including FortiCamera, FortiMail, FortiNDR, FortiRecorder, and FortiVoice. Threat actors are actively exploiting this stack-based buffer overflow in the administrative API to achieve unauthenticated remote code execution. The vulnerability was added to the CISA KEV catalog on May 14, 2025.
In observed exploitation cases, threat actors have performed operations such as scanning the device network, erasing system crashlogs, and enabling fcgi debugging to log credentials or SSH login attempts. Because Fortinet solutions are often deployed on-premises, the onus is on the users to apply security measures. Failure to promptly update and patch systems significantly increases the risk of compromise.
Mitigations
- Follow the vendor’s guidance for updating to the latest version.
- Post-mitigation check for indicators of compromise.
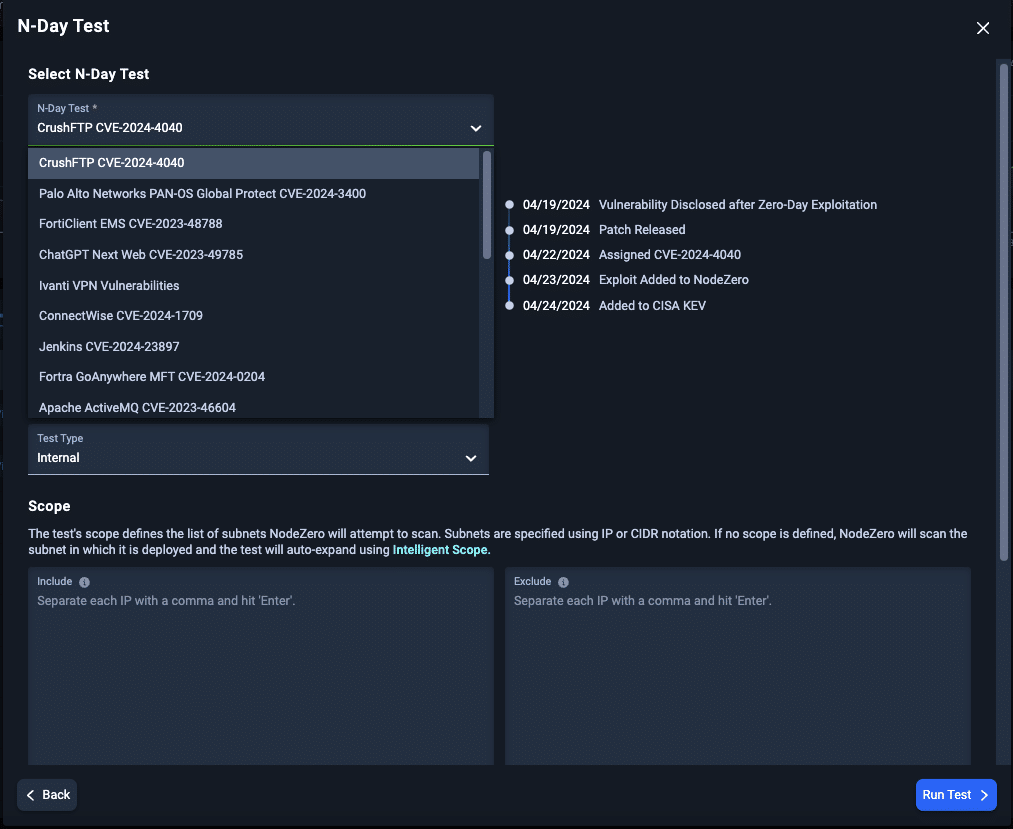
Rapid Response N-Day Testing
🔗 CVE-2025-32756: Low-Rise Jeans are Back and so are Buffer Overflows