Industry Intelligence
SEARCH
CATEGORIES
TAGS
From Patch Tuesday to Pentest Wednesday®: Proof That Redefined Security for a Manufacturer
December 10, 2025
Patch Tuesday is a known event, but attackers are moving faster than ever. For a leading U.S. manufacturer, shifting from simple patching to continuous validation became the key to proving their fixes worked, turning uncertainty into confidence.
Introducing Threat Informed Perspectives: A More Strategic Way to Measure Security Posture
Threat Informed Perspectives give organizations a structured, attacker-aligned way to measure exposure, track real security improvement, and validate remediation over time using continuous, evidence-driven insights from NodeZero.
Endpoint Detection and Response: What It Is and How to Know Yours Is Working
November 24, 2025
EDR tools offer visibility, but visibility isn’t protection. Learn why credential-driven attacks often bypass EDR and how NodeZero validates real-world detection, blocking, and effectiveness across your endpoints.
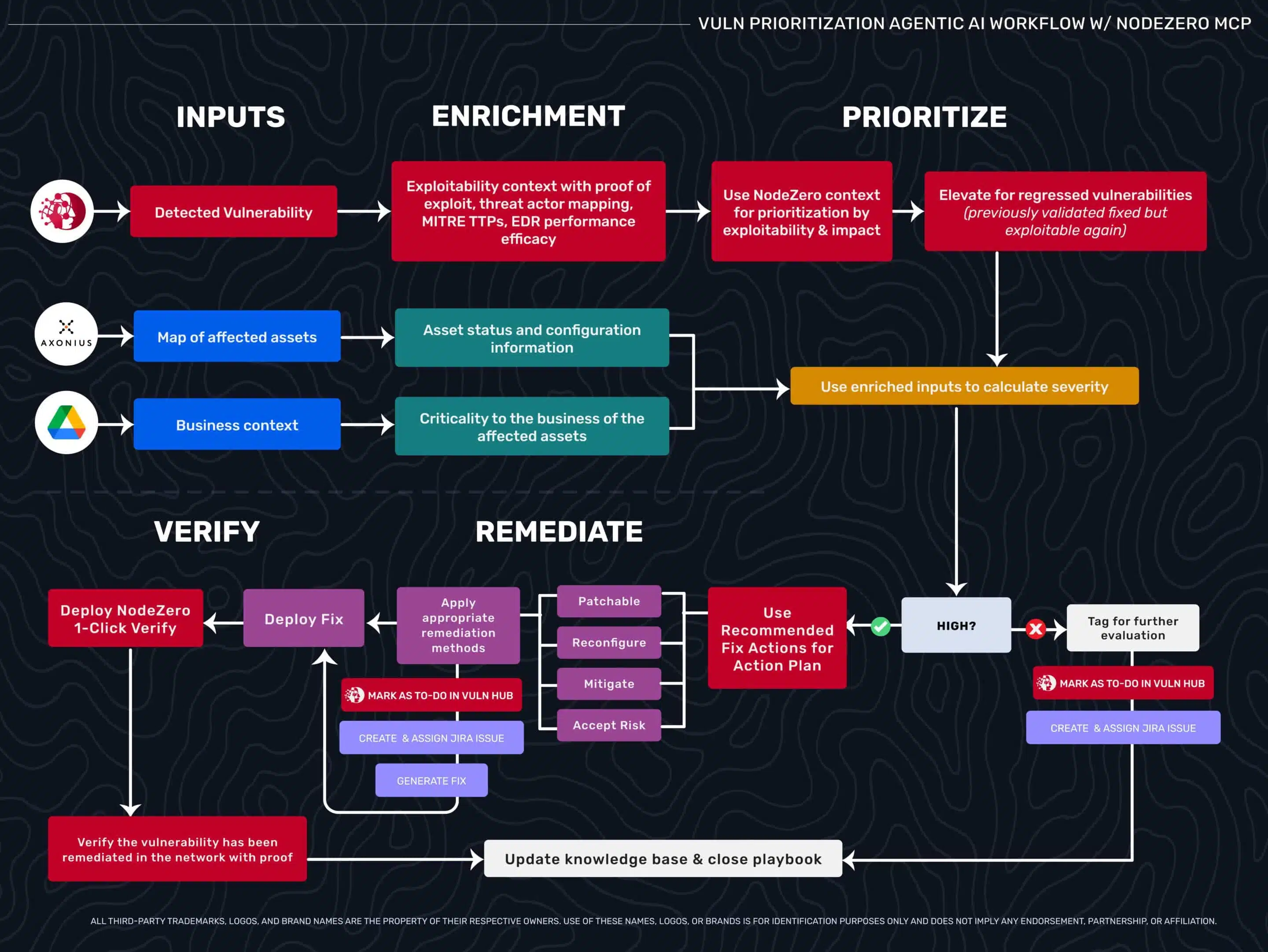
Supercharging Enterprise AI with Real-World Exploitability Data: The NodeZero MCP Server Advantage
Learn how the NodeZero MCP Server supercharges enterprise AI ecosystems with attacker-validated exploitability data, continuous validation, and automated security workflows.
Prioritize What’s Proven: The NodeZero® Approach to Risk‑Based Vulnerability Management
November 18, 2025
Horizon3.ai’s NodeZero® redefines Risk-Based Vulnerability Management by connecting exploitability, business context, and attacker behavior. With new capabilities for High-Value Targeting, Advanced Data Pilfering, Threat Actor Intelligence, and Vulnerability Risk Intelligence, NodeZero moves vulnerability management from noise to proof—helping security teams prioritize, fix, and verify what truly matters.
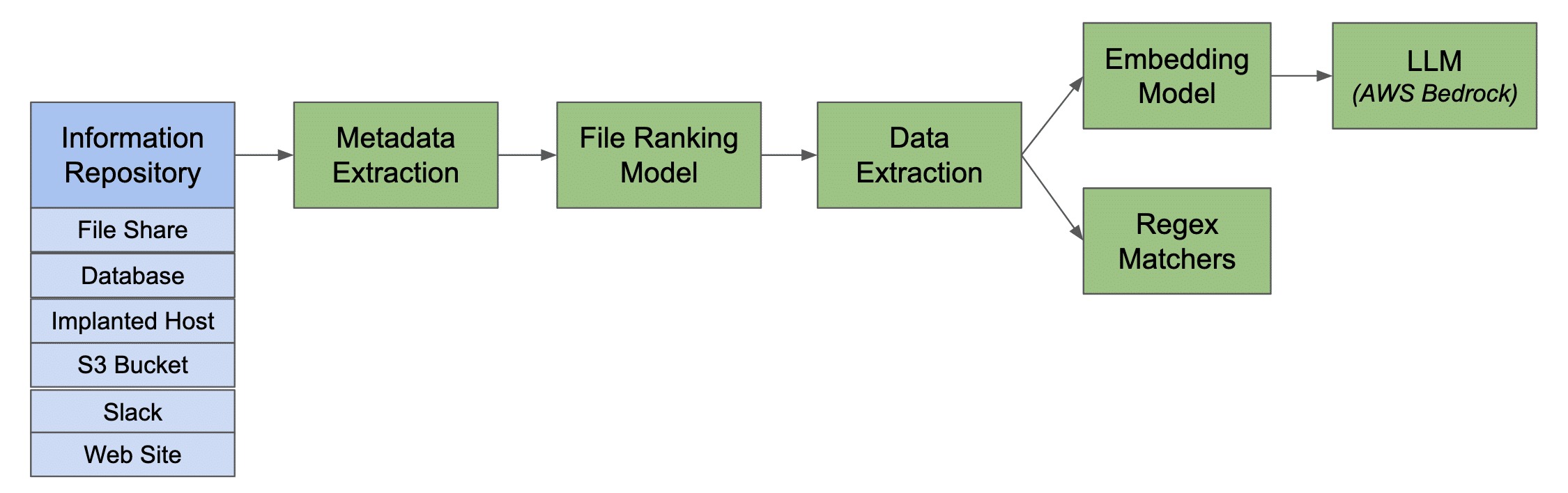
Introducing NodeZero® Advanced Data Pilfering: View Your Data Through the Eyes of an Attacker
NodeZero’s Advanced Data Pilfering uses LLMs to find hidden credentials and classify compromised files—revealing attacker paths and the real business risk in unstructured data.
From Awareness to Assurance: Turning Cybersecurity Awareness Month into a Year-Round Practice
October 29, 2025
Cybersecurity awareness training builds knowledge—but not proof. This post shows how to evolve from education to validation by continuously testing your defenses with NodeZero®. Discover how real-world verification closes policy gaps, exposes hidden risks, and transforms one month of awareness into year-round assurance your security truly works.
Why Open-Source AI Pentesting Could Be Your Next Security Incident
October 23, 2025
Open-source AI pentesting frameworks can unintentionally transmit sensitive pentest data to external LLM APIs, creating hidden security, compliance, and governance risks for enterprises.
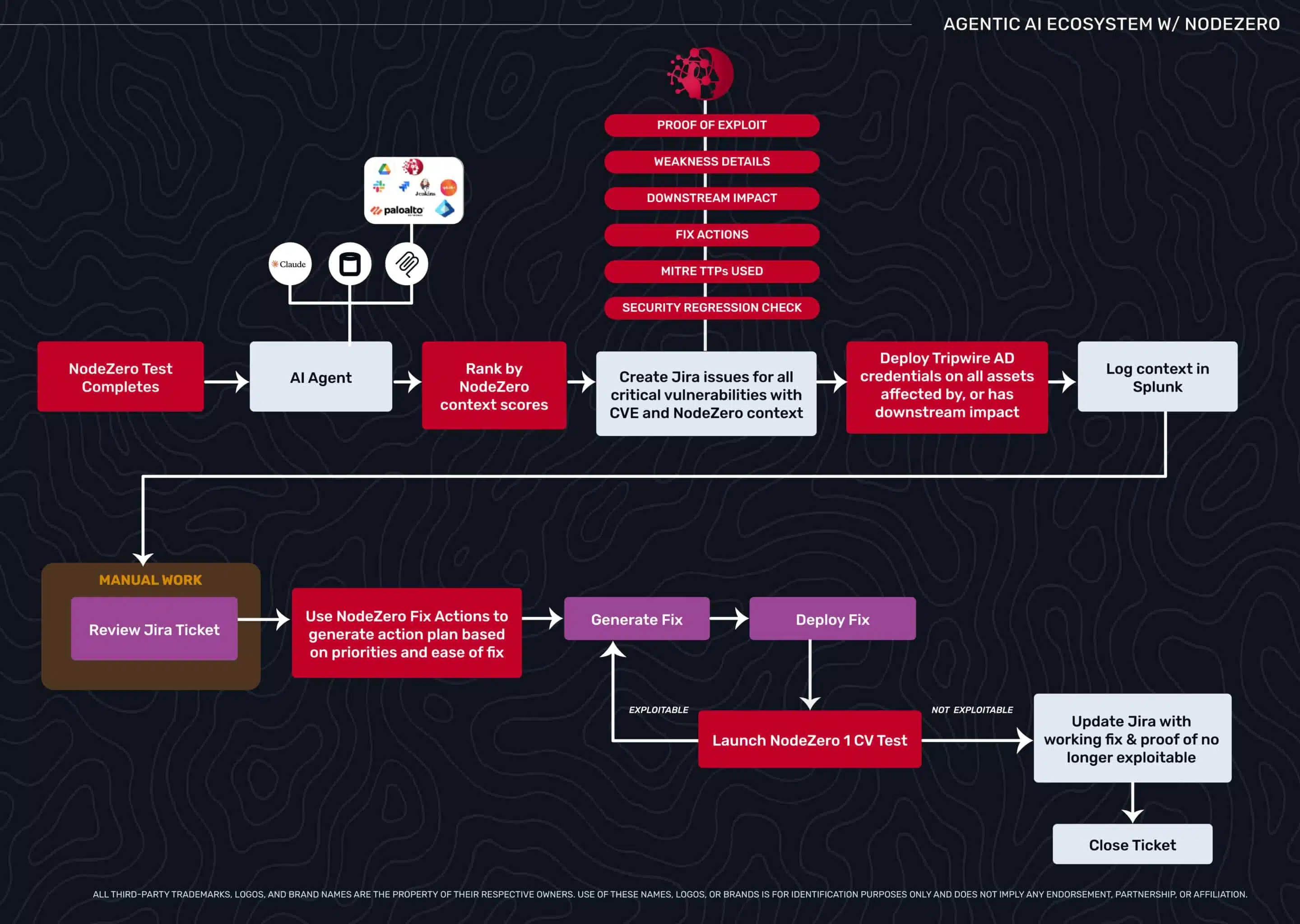
Building FixOps: Architectural Considerations for Autonomous Security Workflows
Designing reliable autonomous security workflows requires more than AI and automation—it demands solid architecture. This guide explores orchestration frameworks, integration points, scaling strategies, and human oversight models that help teams move from prototypes to production-ready FixOps systems built for resilience, precision, and continuous verification at scale.
Beyond Triage: How Exploitability Data Transforms Agentic Security Workflows
Security teams drown in critical CVEs that don’t matter while missing medium flaws that lead to domain admin. This blog explores how exploitability data—validated through autonomous pentesting—enables agentic AI workflows to move beyond triage, prioritize what’s truly exploitable, and automate verification with confidence.