Industry Intelligence
SEARCH
CATEGORIES
TAGS
World Password Day: Credentialed attacks by the numbers
May 5, 2022
It’s World Password Day, but it’s never a bad time to think about credential security and usage. Credentialed attacks are the most popular means of entry into any digital infrastructure, and remain the easiest method of reconnaissance and privilege escalation for bad actors. With some of the most sophisticated open-source attack tools to date, it’s…
“And Then, My EDR Just Watched It Happen”
April 18, 2022
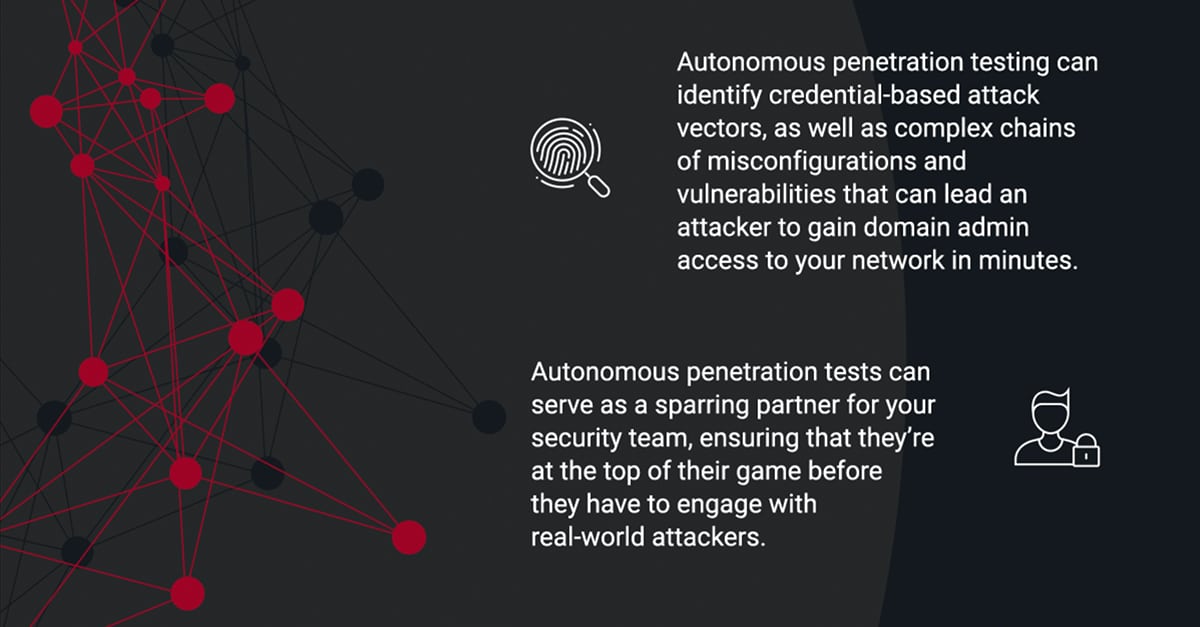
Learn how NodeZero empowers customers to run continuous penetration tests to find vulnerabilities from an attacker’s perspective, to verify fixes after remediation, and hold the EDR and the rest of the security stack accountable for delivering on their capabilities as designed.
Tech Talk: The Attackers Journey Pt. 2
This series centers around how to be an ethical hacker and the steps/processes to get there. In part 2, topics like understanding SQL injection; what SQL injection leads to; why defenders, IT Operators, etc. should care; and so much more were discussed.
SANS Webcast w/ Sponsor Horizon3.ai
Many penetration tests are only point-in-time and/or manual. In this Horizon3.ai sponsored webcast from SANS, take a First Look at how Horizon3.ai’s NodeZero takes on the pen test problem. Listen to SANS Senior Instructor Dave Shackleford and Horizon3.ai’s CEO and Co-Founder Snehal Antani discuss the platform’s highlights and why it might be right for your…
NYIS Meetup Panel, “How do you know it’s fixed?”
David Raviv, host of NYIS Meetup, Snehal Antani, CEO and Co-founder of Horizon3, Steve Ramey of Arete Advisors LLC, and Mark Rasch, computer security and privacy expert, lawyer, author, and commentator, met for a panel discussion over 'How do you know it's fixed?' Learn about: - Employing a defense strategy w/ multiple layers - Identifying…
Tech Talk: The Attackers Journey Pt.1
Join us in side-saddling on an attacker’s journey with Noah King to become an ethical hacker!
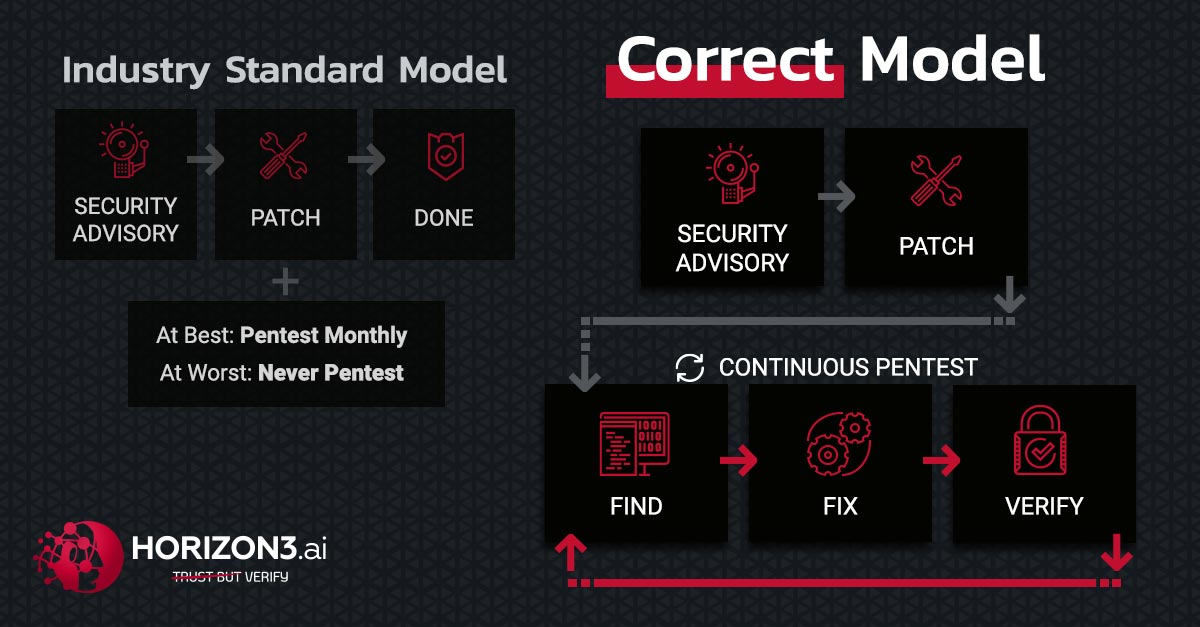
The Industry Standard Model is the Vulnerability
February 11, 2022
Which is more valuable to you; the ability to identify a problem, or the ability to solve the problem? There is a plethora of vulnerability scanning tools that do a decent job identifying vulnerabilities. Unfortunately, those tools rarely discern the possible from the exploitable.
NYIS Fireside Chat with David Raviv
On January 28, 2022, CEO and Co-founder Snehal Antani sat down with host David Raviv of NY Information Security Meetup for an insightful fireside chat. They discussed Snehal's career as former CTO of Splunk and JSOC, his inspiration for starting Horizon3, and his outlook on the future of cyber warfare. Learn about: - Employing a…
Credential Misconfigurations
October 25, 2021
Are your credential policies implemented right? Are your enterprise accounts configured correctly? How do you know? Most phishing, ransomware, and credential attacks start by gaining access to a host and compromising a domain user (Credential Attacks – Horizon3.ai). With a credential in hand, an attacker can persist and pervade, appearing like a legitimate user and…