CVE-2026-35616
Fortinet FortiClient EMS Improper Access Control Vulnerability | Active Exploitation
Fortinet FortiClient Enterprise Management Server (EMS), contains an improper access control vulnerability that can allow an unauthenticated attacker to execute unauthorized code or commands through crafted requests. Fortinet says the flaw has been exploited in the wild. Affected versions are FortiClient EMS 7.4.5 through 7.4.6. Fortinet’s advisory lists the issue as critical and notes a CVSS v3 score of 9.1, while the CVSS score shown by NVD is 9.8. A NodeZero® Proactive Security Platform Rapid Response test is available to help customers verify exposure and confirm remediation.
Technical Details
CVE-2026-35616 is an improper access control issue in the FortiClient EMS API. Fortinet says an unauthenticated attacker can send crafted requests that lead to unauthorized code or command execution. Public reporting has described the issue as a pre-authentication API access bypass that can sidestep authentication and authorization protections. Fortinet also states it has observed exploitation in the wild.
This matters because EMS is the management plane for FortiClient deployments. If an attacker compromises EMS, they are not just landing on a standalone server. They are compromising the system used to manage endpoint security policy across connected devices. That makes this a high-priority exposure for any organization running a vulnerable EMS instance, especially if it is internet accessible.
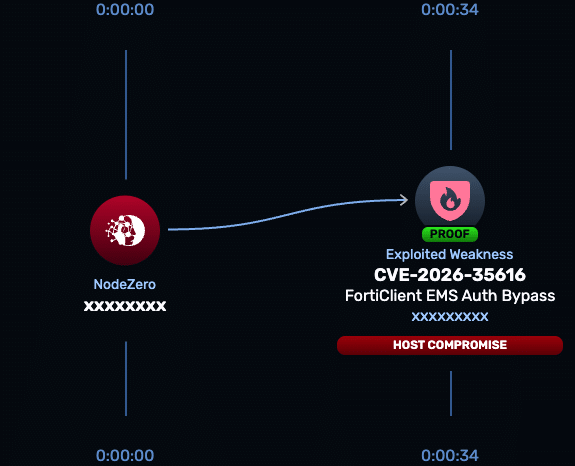
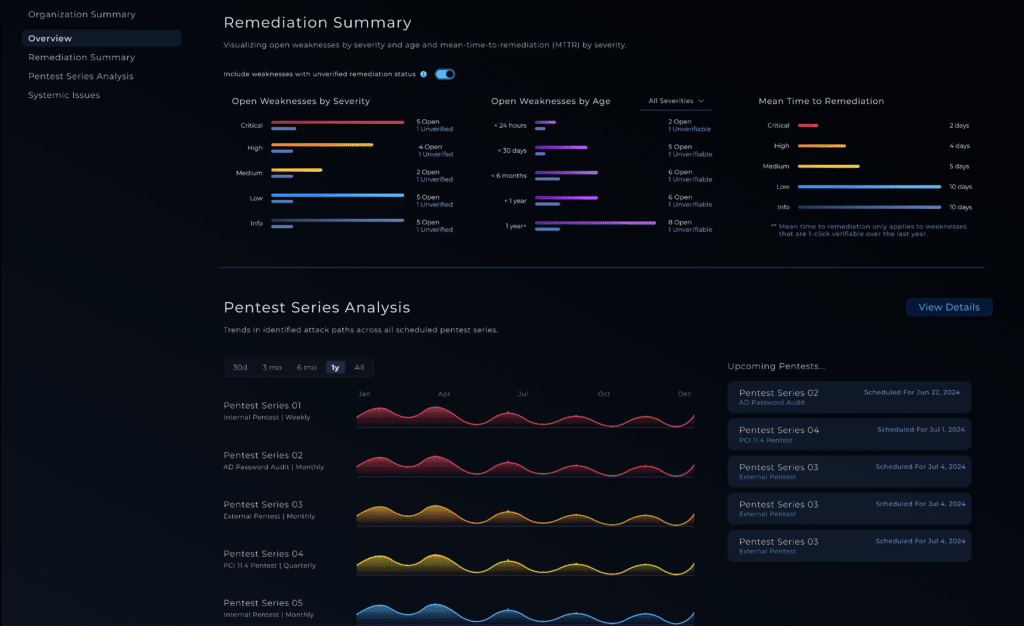
NodeZero® Proactive Security Platform — Rapid Response
A NodeZero Rapid Response test is available now to help organizations quickly determine whether a FortiClient EMS deployment is exposed to CVE-2026-35616 and to validate that remediation removed exploitability.
- Run the Rapid Response test — Horizon3.ai customers can launch the test from the customer portal to verify whether FortiClient EMS is vulnerable to CVE-2026-35616.
- Patch immediately — Fortinet says FortiClient EMS 7.4.5 and 7.4.6 are affected and directs customers to install the vendor hotfixes immediately. Fortinet also says the issue will be fixed in FortiClient EMS 7.4.7. If patching cannot be completed immediately, restrict access to EMS management and agent-facing services to trusted hosts only.
- Re-run the Rapid Response test — confirm the hotfix or upgrade removed exploitability and that the exposed attack path is closed.
Indicators of Compromise
At the time of writing, the public sources tied to this issue confirm active exploitation but do not provide a detailed list of attacker IPs, hashes, filenames, or specific post-exploitation commands. Public reporting does, however, indicate that internet-facing EMS instances have been observed at scale and that exploitation was seen in the wild before broad public disclosure.
| Indicator | Type | Description |
| Crafted requests to vulnerable EMS API endpoints | Activity | Public descriptions characterize the flaw as a pre-authentication API access bypass leading to unauthorized code or command execution. |
| Internet-exposed FortiClient EMS instances | Exposure condition | Shadowserver tracking cited in public reporting found roughly 2,000 exposed EMS instances online, increasing risk for externally reachable systems. |
| Unexplained command execution or system changes on EMS | Behavioral signal | Consistent with Fortinet’s statement that the flaw can enable unauthorized code or command execution. |
Affected versions & patch
- Affected: FortiClient EMS 7.4.5 through 7.4.6. Fortinet states FortiClient EMS 7.2 is not affected.
- Patch: Install the vendor hotfix for 7.4.5 or 7.4.6 immediately, following Fortinet’s release-note instructions. Fortinet says FortiClient EMS 7.4.7 will include a permanent fix.
Timeline
- March 31, 2026 — Public reporting says exploitation attempts were first recorded against honeypots, and Defused Cyber said it observed zero-day exploitation earlier that week.
- April 4, 2026 — Fortinet published advisory FG-IR-26-099 for CVE-2026-35616.
- April 5, 2026 — Media reporting highlighted active exploitation and emergency hotfix guidance.
- April 6, 2026 — Public reporting said CISA added CVE-2026-35616 to the KEV catalog and set an April 9 remediation deadline for FCEB agencies.