CVE-2026-3055
Citrix NetScaler Memory Overread Vulnerability
CVE-2026-3055 is a critical out-of-bounds read vulnerability affecting customer-managed NetScaler ADC and NetScaler Gateway appliances when configured as a SAML Identity Provider. Citrix assigns a CVSS v4.0 score of 9.3 and attributes the issue to insufficient input validation. An unauthenticated remote attacker can exploit this flaw to read sensitive data from appliance memory. Citrix released patches on March 23, 2026, and multiple reports indicate that exploitation activity has already begun.
Technical Details
Citrix describes CVE-2026-3055 as a memory overread vulnerability caused by improper input validation in NetScaler ADC and Gateway when operating as a SAML IdP.
The vulnerability does not require authentication or user interaction. An attacker can send crafted requests to a vulnerable appliance to trigger memory disclosure. Because the issue allows reading process memory, attackers may extract sensitive information such as session data or other credentials that can be used for follow-on access.
The exposure is configuration-dependent. Only systems configured as a SAML Identity Provider are affected. Citrix explicitly notes that Citrix-managed cloud services are not impacted.
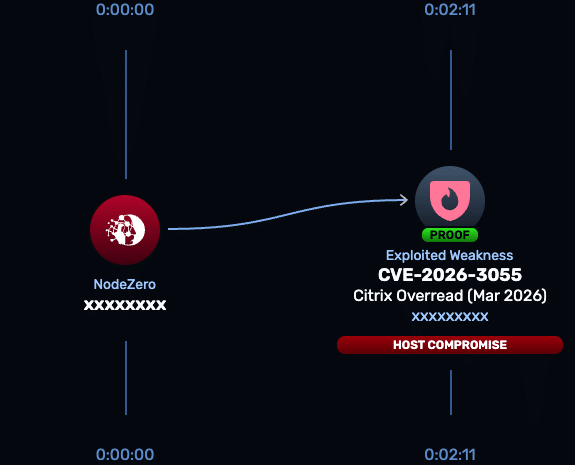
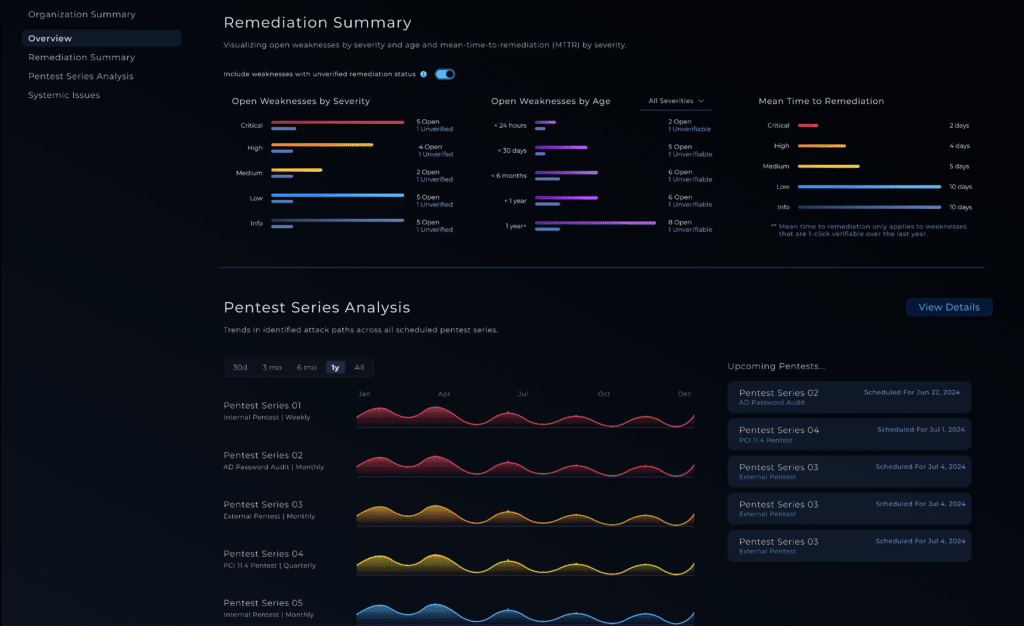
NodeZero® Proactive Security Platform — Rapid Response
The Rapid Response test in NodeZero is designed to help security teams answer the question that matters most: is this actually exploitable in our environment? For CVE-2026-3055, the test can be used to validate exposure before remediation and confirm the issue is no longer exploitable after the fix is applied.
- Run the Rapid Response test
Use NodeZero to verify whether NetScaler instances configured as a SAML IdP are susceptible to unauthenticated memory disclosure. - Patch immediately
Citrix has released fixed versions for affected NetScaler ADC and Gateway deployments. Organizations should upgrade to the latest supported releases, including:
- 14.1-60.58 or later
- 14.1-66.59 or later
- 13.1-62.23 or later
- 13.1-FIPS / NDcPP 13.1-37.262 or later
- Customers should also review configurations to determine whether the appliance is operating as a SAML IdP.
- Re-run the Rapid Response test
After patching, re-test to confirm the vulnerability is no longer exploitable and that remediation was effective.
Indicators of Compromise
Citrix has not published a formal list of indicators such as attacker IP addresses, file hashes, or filenames for CVE-2026-3055.
However, based on the exploit behavior described, defenders should monitor for:
- Suspicious or malformed requests targeting NetScaler appliances configured as SAML IdP
- Repeated probing activity against authentication endpoints
- Signs of session data exposure or anomalous authentication behavior
- Unusual access patterns involving externally exposed NetScaler systems
Reports from security researchers indicate that repeated crafted requests can return different segments of memory, which may be used to extract sensitive data over time.
Affected versions & patch
Affected:
- NetScaler ADC and NetScaler Gateway 14.1 before 14.1-60.58
- NetScaler ADC and NetScaler Gateway 13.1 before 13.1-62.23
- NetScaler ADC FIPS and NDcPP before 13.1-37.262
Patch:
- Upgrade to 14.1-60.58 or later supported releases
- Upgrade to 14.1-66.59 or later supported releases
- Upgrade to 13.1-62.23 or later supported releases
- Upgrade to 13.1-FIPS / NDcPP 13.1-37.262 or later
Citrix recommends verifying whether the system is configured as a SAML IdP by checking for the presence of SAML IdP profiles in the configuration.
Timeline
- March 23, 2026: Citrix published CTX696300 and disclosed CVE-2026-3055.
- March 27, 2026: Security reporting indicates researchers observed active reconnaissance against vulnerable NetScaler instances.
- March 30, 2026: Public reporting confirms active exploitation has begun.
References
- BleepingComputer Article: Citrix urges admins to patch NetScaler flaws as soon as possible
- Citrix Security Bulletin CTX696300: NetScaler ADC and NetScaler Gateway Security Bulletin for CVE-2026-3055 and CVE-2026-4368
- Rapid7 Vulnerability Database Entry: CVE-2026-3055: Citrix NetScaler ADC and NetScaler Gateway Out-of-Bounds Read
- CERT-EU Security Advisory 2026-003: Multiple Vulnerabilities in Citrix NetScaler and Citrix ADC
- SecurityWeek Coverage: Critical Citrix NetScaler Vulnerability Poised for Exploitation