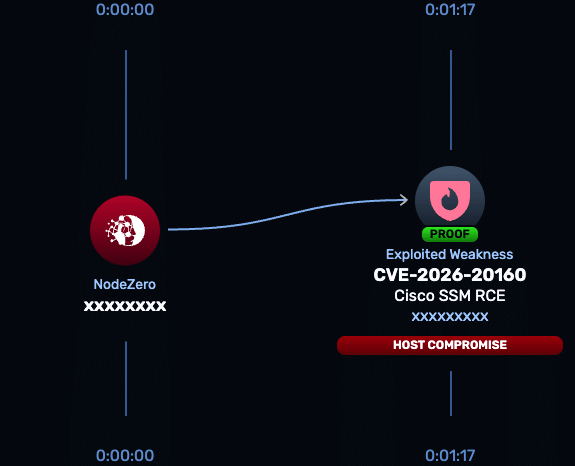
CVE-2026-20160
Cisco Smart Software Manager On-Prem Arbitrary Command Execution Vulnerability
A vulnerability in Cisco Smart Software Manager On-Prem (SSM On-Prem) could allow an unauthenticated, remote attacker to execute arbitrary commands on the underlying operating system with root-level privileges. The issue is caused by the unintended exposure of an internal service that can be accessed via a crafted API request. Cisco rates this vulnerability as Critical with a CVSS 3.1 score of 9.8 and states there are no workarounds.
Technical Details
Cisco Smart Software Manager On-Prem is designed for organizations that manage Cisco software licenses locally without allowing direct communication to Cisco over the internet. As a result, it is typically deployed inside trusted management networks.
CVE-2026-20160 is an unauthenticated remote command execution vulnerability. The root cause is the unintended exposure of an internal service. An attacker can send a crafted request to the exposed API endpoint and execute commands as root on the underlying host.
Successful exploitation grants full control of the SSM On-Prem appliance. Because the system manages licensing and deployment metadata and operates within a trusted network segment, compromise provides a high-privilege foothold that can be used for lateral movement, persistence, and access to sensitive operational data.
Cisco has confirmed:
- Patching is required to remediate
- No authentication is required
- Exploitation results in root-level command execution
- No workarounds are available
NodeZero® Proactive Security Platform — Rapid Response
The NodeZero Rapid Response test for CVE-2026-20160 validates whether Cisco Smart Software Manager On-Prem is exploitable in your environment. The test safely exercises the exposed service to determine if unauthenticated command execution is possible.
- Run the Rapid Response test: Launch from the platform to verify exposure.
- Patch immediately: Cisco requires upgrading to a fixed release; no workarounds exist.
- Re-run the Rapid Response test: Confirm that exploitation is no longer possible after remediation.
Rapid Response tests are developed by Horizon3.ai’s research team through reverse engineering and safe exploit development to validate real-world risk.
Affected versions & patch
- Affected: Cisco Smart Software Manager On-Prem releases 9-202502 through 9-202510
- Not affected: Releases earlier than 9-202502
- Fixed: Release 9-202601 and later
- Workarounds: None
Cisco states that upgrading to the fixed release is the only remediation.
Timeline
- April 1, 2026: Cisco publishes advisory for CVE-2026-20160
- April 1, 2026: CVE record published
- April 8, 2026: Horizon3.ai research team reverses the vulnerability and releases Rapid Response coverage