Cloud
SEARCH
CATEGORIES
TAGS
Preemptive Exposure Management Is the Goal. Autonomous Attack Validation Is How You Get There.
March 4, 2026
Reacting to cyberattacks has never been a winning strategy. Most organizations know this, yet many still find themselves responding after the fact, investigating incidents, explaining impact, and rebuilding trust with leadership. What’s changed is a growing recognition that risk must be reduced before attackers act, not measured after the damage is done. That’s the promise…
When “Read-Only” Isn’t: K8s nodes/proxy GET to RCE
February 27, 2026
A Kubernetes service account with “read-only” nodes/proxy GET permission can execute arbitrary commands across pods via the kubelet API. This post breaks down how WebSocket behavior turns monitoring access into cluster-wide RCE—and how NodeZero detects it.
Mastering Cloud Security: Uncovering Hidden Vulnerabilities with NodeZero™
August 21, 2024
Master cloud security with NodeZero™ Cloud Pentesting. Easily uncover vulnerabilities across AWS and Azure, prioritize identity risks, and secure your environment in just minutes. Stay ahead of threats.
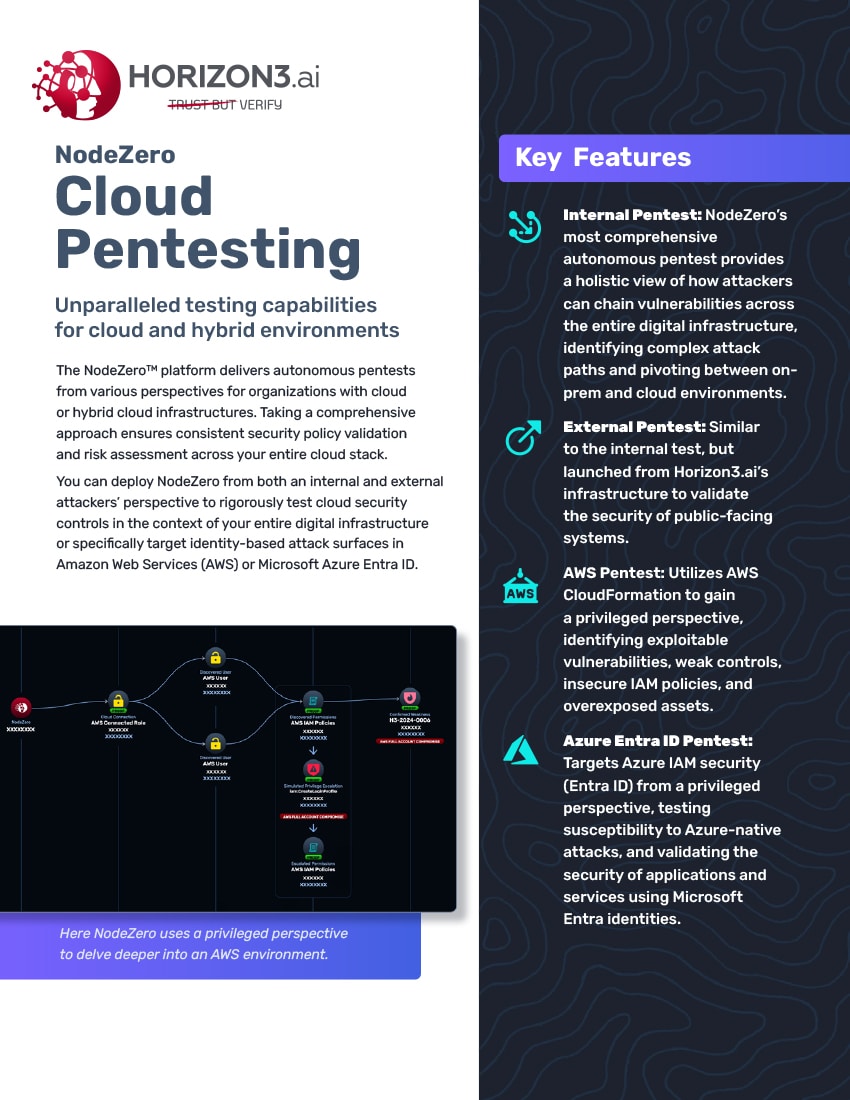
NodeZero Cloud Pentesting
July 29, 2024
NodeZero Cloud Pentesting offers autonomous, comprehensive pentests for cloud and hybrid environments, validating security policies and assessing risks from internal and external perspectives. It rigorously tests cloud security controls in AWS and Microsoft Azure Entra ID, identifying vulnerabilities, misconfigurations, and potential attack paths. This approach ensures thorough validation of security defenses and highlights connections between…