Cyber Readiness During Escalating Geopolitical Conflict
Recent activity suggests Iranian cyber operators are shifting toward a more decentralized and opportunistic model of cyber operations.
Industries such as energy, financial services, telecommunications, manufacturing, healthcare, and the defense supply chain should expect to face increased targeting because they operate systems that modern economies depend on.
The most effective response is not speculation or alarm.
It is preparedness grounded in real adversary tradecraft.
What You Need to Know Now
Our latest analysis examines the operational patterns emerging in recent Iranian cyber campaigns and outlines the defensive priorities organizations should focus on today.
Key topics covered include:
- Why Iranian cyber operations increasingly resemble distributed cyber “guerrilla warfare”
- The technical tradecraft these operators consistently rely on
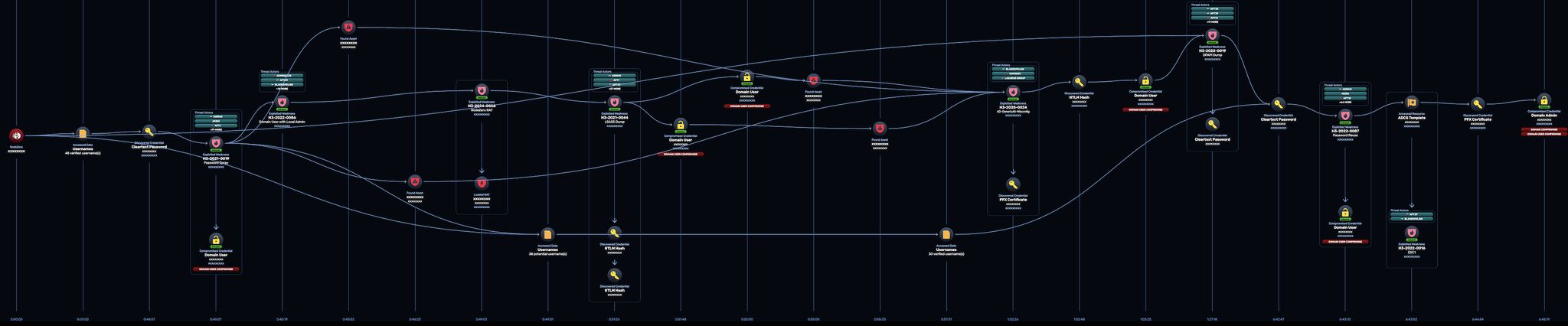
- How attackers move from internet exposure to enterprise-wide compromise
- The systems most likely to be targeted for maximum operational disruption
- Practical steps security leaders can take to improve resilience immediately
Understanding the Threat Landscape
Iranian cyber operators have demonstrated consistent operational patterns across multiple campaigns. While tooling evolves, several technical behaviors repeatedly appear.
Edge Infrastructure Exploitation
- Iranian operators have repeatedly weaponized vulnerabilities in internet-facing infrastructure, often within days of disclosure.
- Once inside a network, Iranian operators consistently pivot toward identity infrastructure.
- Operational technology and critical infrastructure is a growing focus because it can produce significant disruption with minimal effort.
- Supply chain, service provider, and remote management platforms represent access to downstream organizations.
Keeping Your Organization Resilient
Early preparation is key to maintaining and proving resilience before and during an attack. Based on observed Iranian TTPs, there are concrete steps you can take today.
- Test and identify exposure across internet-facing infrastructure and applications
- Test and strengthen identity security
- Test and validate detection against real adversary TTPs
- Rehearse and train incident response under realistic conditions
- Make recovery a core defensive capability
Preparation today determines resilience tomorrow.

How Horizon3 Helps Protect Our Customers
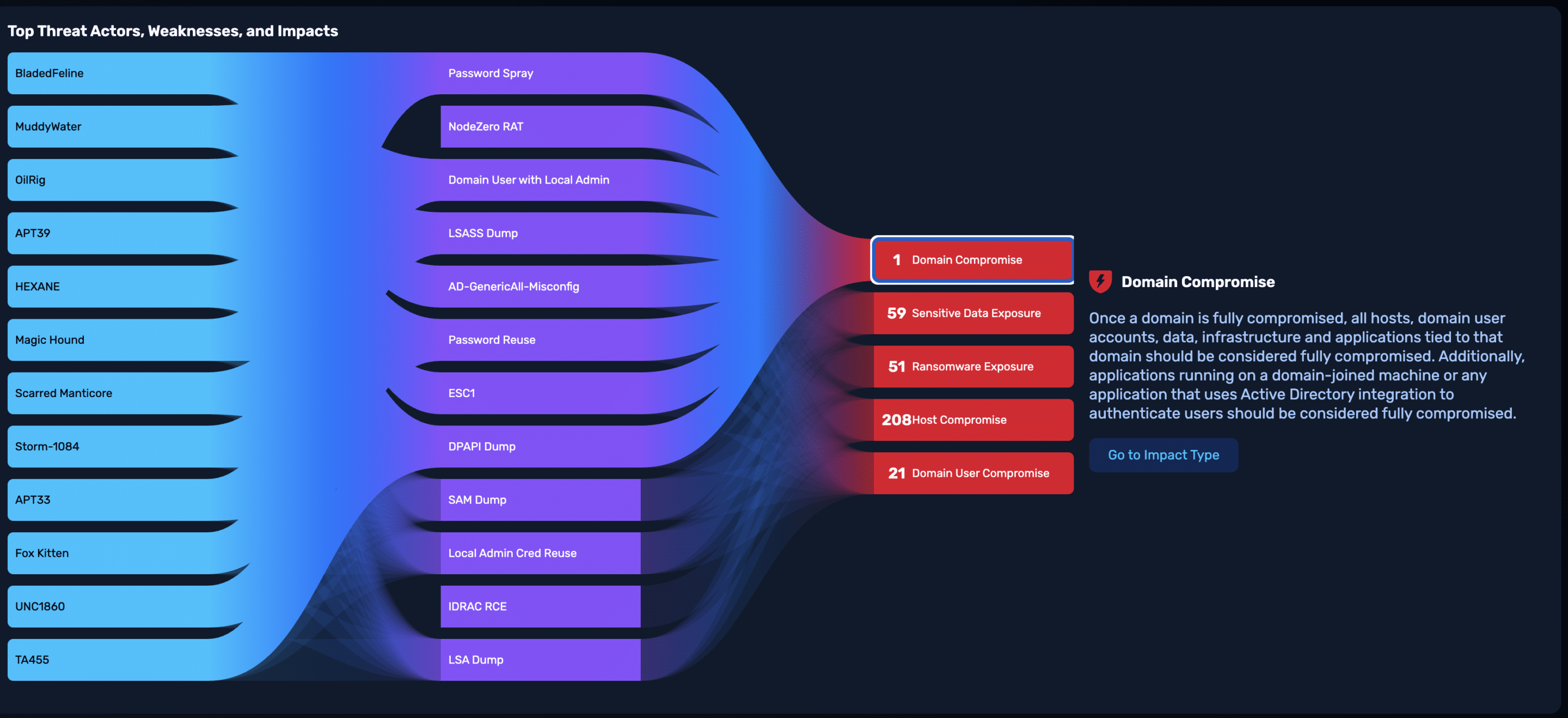
Our AI Hacker – NodeZero – has 100% coverage of Iranian cyber tactics and is able to quickly assess how Iranian threat actors could compromise an organization. Right now is a crucial moment to help our customers, prospects and partners harden their businesses against forthcoming Iranian attacks, and given the urgency, we’re surging resources to assist these businesses however possible. As the only technology in the world capable of conducting these assessments at scale, we don’t take that claim or responsibility lightly given global events and our history of national service.
We announced on March 13, 2026 that we have extended our Threat Actor Intelligence for Iranian threat actors to all Horizon3 customers at no charge for the next 30 days. We believe this ongoing threat is a significant escalation, and we are ready to stand with our customers to help them the best way we can, arming them with the best information and tools we have to identify how and where they are potentially exposed so they can take the steps necessary to close off those critical attack paths before they are exploited.
Learn more about Threat Actor Intelligence.
Research and Resources
Security leaders seeking deeper technical analysis can explore the following research produced alongside this page.
Iranian APT TTP Report
A detailed technical analysis of the tactics, techniques, and procedures used by Iranian cyber operators, including common initial access vectors, identity compromise methods, and operational targeting patterns.
Iranian Cyber Activity Briefing
An executive-focused overview of current activity patterns and recommended actions security leaders can take to improve resilience.
Threat Actor Intelligence Documentation
See how Threat Actor Intelligence highlights which attack paths are most likely to be used by Iranian threat actors to attempt to gain access to your environment.
To learn more check out our blog When Conflict Extends Into Cyberspace: What Security Leaders Should Expect.