Industry Intelligence
SEARCH
CATEGORIES
TAGS
What is Zero Trust – and How NodeZero Can Help
October 13, 2022
Zero Trust. Everyone’s talking about it, but what does it truly mean, and how can you prove that your organization is using a Zero Trust model effectively?
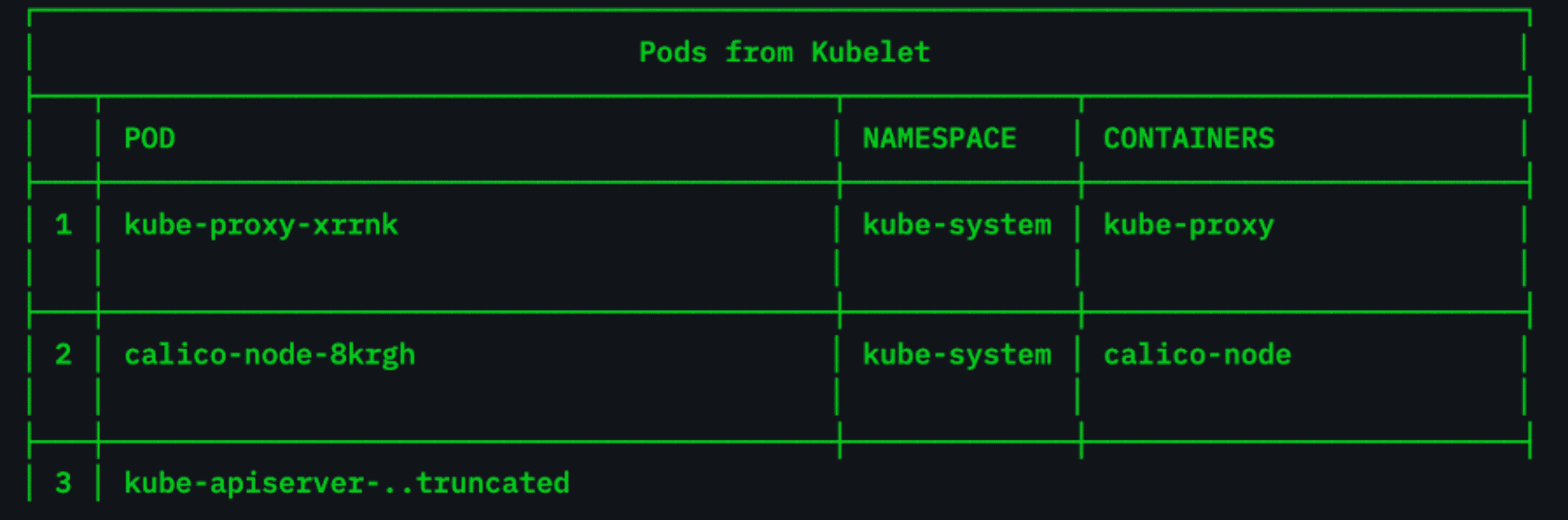
Are Your Kubernetes Clusters Configured Properly?
August 31, 2022
Researchers recently discovered some 900,000 Kubernetes clusters that were potentially exposed to malicious scans and data theft during a threat-hunting exercise.
Tech Talk: The Attackers Journey Pt. 6
Noah King, one of Horizon3's front-end developers, is inviting you into his experience as he learns to be an expert at ethical hacking and get his OSCP cert!
Go Hack Yourself: 5 Crazy Ways NodeZero Became Domain Admin
Attackers don't have to "hack in" using zero-day vulnerabilities. Often, attackers log in by chaining together misconfigurations, dangerous product defaults, and exploitable vulnerabilities to harvest and reuse credentials. This session will discuss five real-world attacks that enabled Horizon3.ai to become domain administrator, gain access to sensitive data, take over cloud VPCs, and compromise critical business…
An International Look at Cybercrime
August 29, 2022
Authoritarian regimes have learned in recent years that cybercrime can be a profitable economic enterprise – so much so that they continue to invest substantial resources in large- and small-scale cybercrime.
Beyond Password Issues: How NodeZero Found Access to an Organization’s Azure Cloud Environment
August 25, 2022
NodeZero is a generational leap beyond a traditional pentest – organizations often see that for themselves from the moment they give our autonomous pentesting platform a shot. NodeZero surfaces risks and weaknesses that would never have come up during a general vulnerability scan as it chains together attack tactics and techniques to illuminate your most…
The Attackers Perspective Through Splunk Data & Workflows
As the industry accelerates toward a threat landscape of attack and defense by algorithm and machine, humans must run at machine speed to manage the stakes of tool misconfiguration, mishandling of logs, and missed patching opportunities. The NodeZero app for Splunk is a force multiplier—combining attacker insights into your unique environment with your existing Splunk…
One Weak Password Leads to Compromise
August 17, 2022
NodeZero, discovered a customer’s host that had not appeared in previous pentests due to a small change in their configuration.
Tech Talk: The Attackers Journey Pt. 5
In this session, Noah and his mentors will not only explore why the Kerberoasting attack technique is so pervasive and how you can configure Kerberos better to avoid these attacks, but also alternative setups that allow you to avoid Kerberoasting altogether.
Webinar: External Autonomous Pentesting
With the announcement of the addition of external penetration testing capabilities to NodeZero, Horizon3.ai is hosting a webinar to introduce this enhancement to our autonomous penetration testing platform. This extension of NodeZero’s capabilities makes Horizon3.ai the first cybersecurity company to offer both internal and external penetration testing in one self-service platform. Join Naveen Sunkavally, Horizon3.ai’s…