Blogs
SEARCH
CATEGORIES
TAGS
Insight – Horizon3.ai Annual Review Snapshot 2022
January 8, 2023
Over the past year, Horizon3.ai pentests revealed cybersecurity vulnerability trends across multiple industry sectors around the globe.
Get the Most From TrendMicro Apex One EDR with NodeZero
December 12, 2022
Learn how you can use NodeZero to get the Most From TrendMicro Apex One EDR, ensuring you stop, alert, log, and detect activity by bad actors.
Holiday Season Threat Awareness
November 23, 2022
As we approach the holiday season, it is important that our customers remain stay and continue a regular cadence of autonomous pentests. Although it’s the time of year for holiday cheer, we’ve seen cyber threat actors (CTAs) take advantage of lackadaisical company manning and low staff.
Verifying Credentialed Access to Your Hybrid Cloud Sprawl Matters More Than Ever
November 1, 2022
Verifying credentialed access to your hybrid cloud sprawl matters more than ever. See example attack paths to understand risks to AWS cloud.
The Undeniable Effectiveness of Password Spray
October 20, 2022
One of the most effective techniques NodeZero employs for initial access is password spray. It's a primitive technique, basically guessing passwords, and when it works it feels like magic. Yet we see it work time and time again in various pentests conducted by NodeZero. In this post we'll talk about what password spray is and…
Secure Your Fortinet Appliances Across On-Prem, Cloud, and Hybrid Networks at Scale
October 18, 2022
Learn how to use NodeZero from Horizon3.ai to secure your Fortinet appliances across on-prem, cloud, and hybrid networks at scale.
What is Zero Trust – and How NodeZero Can Help
October 13, 2022
Zero Trust. Everyone’s talking about it, but what does it truly mean, and how can you prove that your organization is using a Zero Trust model effectively?
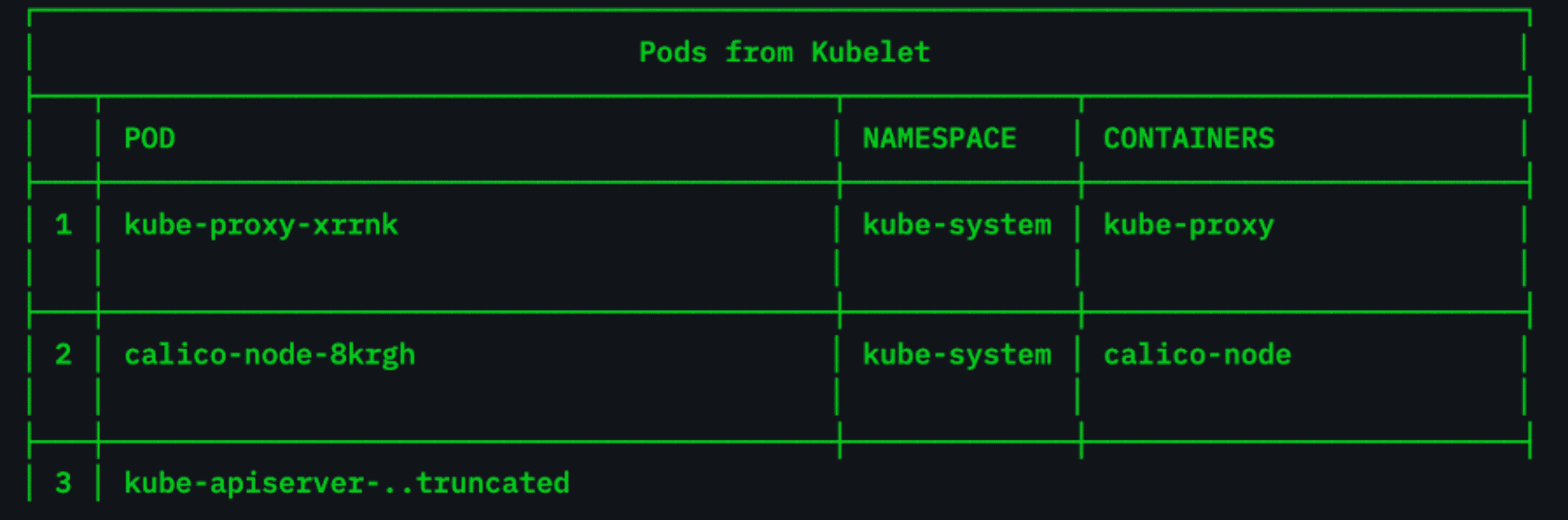
Are Your Kubernetes Clusters Configured Properly?
August 31, 2022
Researchers recently discovered some 900,000 Kubernetes clusters that were potentially exposed to malicious scans and data theft during a threat-hunting exercise.
An International Look at Cybercrime
August 29, 2022
Authoritarian regimes have learned in recent years that cybercrime can be a profitable economic enterprise – so much so that they continue to invest substantial resources in large- and small-scale cybercrime.
Beyond Password Issues: How NodeZero Found Access to an Organization’s Azure Cloud Environment
August 25, 2022
NodeZero is a generational leap beyond a traditional pentest – organizations often see that for themselves from the moment they give our autonomous pentesting platform a shot. NodeZero surfaces risks and weaknesses that would never have come up during a general vulnerability scan as it chains together attack tactics and techniques to illuminate your most…