Research Blog
Welcome to our cybersecurity research blog where we uncover how malicious actors exploit weaknesses in systems, while going beyond the technical aspects and examining real-world perspectives across various industries.
Here you’ll find extensive research and insight from the well-known Horizon3.ai attack team, intuitive perspectives on everything security, and real-world attack path short stories that come directly from discoveries made by NodeZero.
Filters
Showing 151–156 of 161 results
ProxyShell: More Ways for More Shells
In August, Orange Tsai released details and also spoke at BlackHat and DEFCON detailing his security research into Microsoft Exchange. His latest blog post details a series of vulnerabilities dubbed ProxyShell. ProxyShell is a chain of three vulnerabilities: CVE-2021-34473 – Pre-auth Path Confusion leads to ACL Bypass CVE-2021-34523 – Elevation of Privilege on Exchange PowerShell Backend CVE-2021-31207 – Post-auth Arbitrary-File-Write leads to RCE The research detailed a...
Read More Product Updates from our CTO
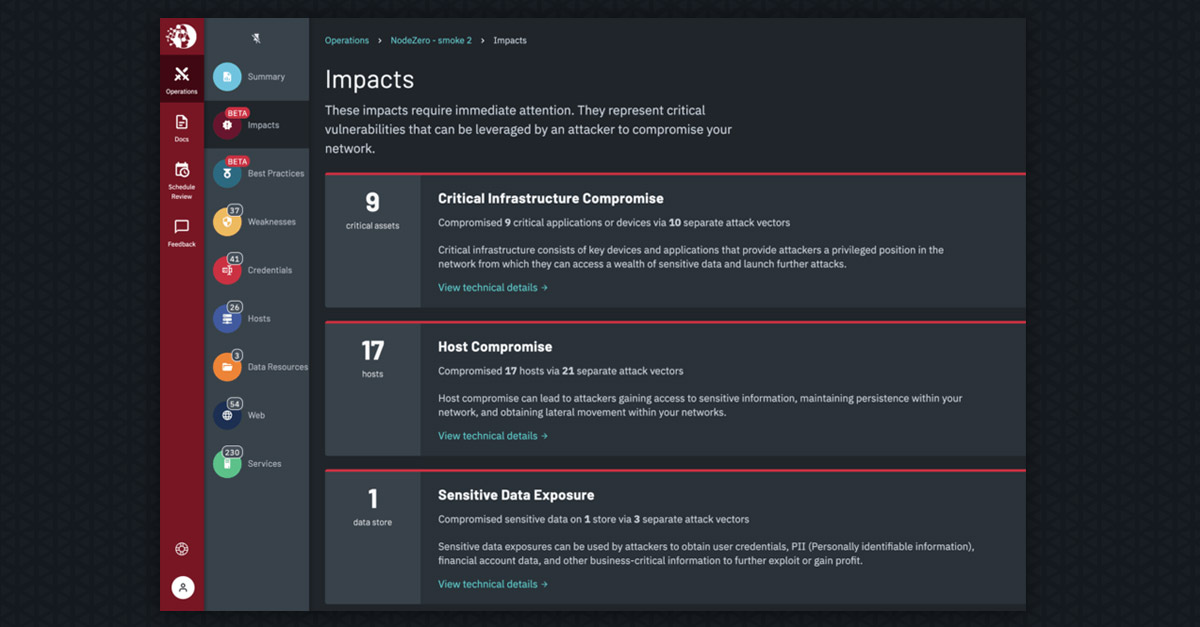
The engineering team has been working tirelessly to improve the “what to wow” user experience, add more attack content, add indicators of best practices and improve analytical insights. Improving our “what to wow” user experience – In security, there are two types of findings: critical problems that require you skip lunch, or cancel plans with your family, to urgently fix...
Read More Be Open to Be Wow’d
Being a #learnitall, Lesson 1: Be Open to Be Wow’d Most of the startup advice out there is pretty clear: get feedback early and often. Customer input is invaluable to delivering iter0, your MVP, feature releases that matter, bug fixes, utility and simplicity. In Customer Success, a lot of the job is review and advise so a customer can hit their...
Read More Tech Talk: Compliance in Security
In the world of network security, compliance is the bare minimum. Compliance is locking your door, but what about your windows?
Read More CVE-2021-27927: CSRF to RCE Chain in Zabbix
Zabbix is an enterprise IT network and application monitoring solution. In a routine review of its source code, we discovered a CSRF (cross-site request forgery) vulnerability in the authentication component of the Zabbix UI. Using this vulnerability, an unauthenticated attacker can take over the Zabbix administrator's account if the attacker can persuade the Zabbix administrator to follow a malicious link....
Read More POC CVE-2021-21972
Write the file supplied in the --file argument to the location specified in the --path argument. The file will be written in the context of the vsphere-ui user. If the target is vulnerable, but the exploit fails, it is likely that the vsphere-ui user does not have permissions to write to the specified path.
Read More