Resource Center
Welcome to our cybersecurity resource center where we uncover how malicious actors exploit weaknesses in systems, while going beyond the technical aspects and examining real-world perspectives across various industries.
LATEST VULNERABILITIES
Cisco IOS XE Wireless Controller Software Arbitrary File Upload Vulnerability
Read More →WEBINAR REPLAY
SEARCH
CATEGORIES
TAGS
SEARCH
CATEGORIES
TAGS
Apache ActiveMQ RCE Leads to Domain Compromise
December 1, 2023
Pervasive CISA Known Exploited Vulnerability Enables Initial Access
Insight – Holiday Threat Awareness 2023
December 1, 2023
Amidst the hustle and bustle of holiday preparations and last-minute shopping, cybercriminals often take advantage of the increased online activity and spending complacency of individuals and businesses...
Fireside Chat: Horizon3.ai and F12.net
Stephen Gates, Principal Security SME at Horizon3.ai and Calvin Engen, Chief Technology Officer, and Managing Partner of F12.net discuss: - Why there is a such growing demand for managed cybersecurity services. - What’s helping F12 clients meet and exceed cybersecurity standards and best practices. - Where Calvin thinks the security industry is headed and what…
Cisco IOS XE CVE-2023-20198: Deep Dive and POC
October 30, 2023
Introduction This post is a follow up to https://horizon3.ai/attack-research/attack-blogs/cisco-ios-xe-cve-2023-20198-theory-crafting/. Previously, we explored the patch for CVE-2023-20273 and CVE-2023-20198 affecting Cisco IOS XE and identified some likely vectors an attacker might have used to exploit these vulnerabilities. Now, thanks to SECUINFRA FALCON TEAM's honeypot, we have further insight into these vulnerabilities. POC See below for an…
Cisco IOS XE CVE-2023-20198 and CVE-2023-20273: WebUI Internals, Patch Diffs, and Theory Crafting
October 25, 2023
Introduction There has been a lot of news around the recent Cisco IOS XE vulnerabilities CVE-2023-20198 and CVE-2023-2073. Information about this vulnerability was first published by Cisco on October 16th, 2023, and since then we have seen evidence of mass exploitation and implantation. In this post we share our technical insights so far into these…
NextGen Mirth Connect Remote Code Execution Vulnerability (CVE-2023-43208)
October 25, 2023
Mirth Connect, by NextGen HealthCare, is an open source data integration platform widely used by healthcare companies. Versions prior to 4.4.1 are vulnerable to an unauthenticated remote code execution vulnerability, CVE-2023-43208. If you’re a user of Mirth Connect, you’ll want to upgrade to the latest patch release, 4.4.1, as of this writing.
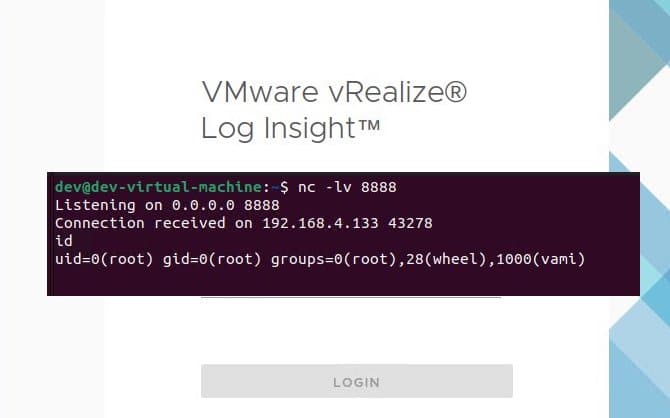
VMware Aria Operations for Logs CVE-2023-34051 Technical Deep Dive and IOCs
October 20, 2023
Introduction This report is a follow up to https://horizon3.ai/vmware-vrealize-log-insight-vmsa-2023-0001-technical-deep-dive/. Earlier this year we reported the technical details for VMSA-2023-0001 affecting VMware Aria Operations for Logs (formerly VMware vRealize Log Insight). In that report, we showed how an attacker could use three different CVEs to achieve remote code execution. During the course of that investigation, we…
Cisco IOS XE Web UI Vulnerability: A Glimpse into CVE-2023-20198
October 19, 2023
On Monday, 16 October, Cisco reported a critical zero-day vulnerability in the web UI feature of its IOS XE software actively being exploited by threat actors to install Remote Access Tools (RATs) and backdoor vulnerable devices exposed on the internet.
The Art Of Attack—Enhancing Defense Strategies: Unleashing The Power Of Autonomous Pen Testing | A Brand Story Conversation From Black Hat USA 2023 | An Horizon3.Ai Story With Snehal Antani
October 12, 2023
A Brand Story Conversation With Sean Martin And Snehal Antani, Co-Founder & CEO At Horizon3.ai
Tech Talk: Journey to OSCP
Horizon3.ai Senior Engineer Noah King discusses the journey of obtaining an Offensive Security Certified Professional (OSCP) certification. Whether you're a cybersecurity enthusiast or a beginner looking to explore the field, you'll learn tips and tricks to help you navigate the certification process, including: - How to get started in Offensive Security with little or no…